Researchers at Cisco Talos have come across an attack that combines two Microsoft Office exploits, one old and one new, likely in an effort to avoid detection.
One of the exploits leverages CVE-2017-0199, an Office vulnerability patched by Microsoft in April with its monthly security updates. The security hole had been exploited in attacks before Microsoft released a fix. An exploit has since been added to the toolkits of numerous threat groups, including cybercriminals and cyberspies linked to China and Iran.
In the attacks observed by Cisco Talos, CVE-2017-0199 was used in combination with CVE-2012-0158, an old Office flaw that is still exploited in many campaigns.
The cybercriminals have apparently attempted to use these vulnerabilities to deliver the Lokibot banking Trojan. The attack also drops an older version of Ramnit, but experts believe a Ramnit infection component may have been picked up by accident somewhere along the way.
While the combination of exploits did not work as intended during Cisco’s tests, researchers have analyzed the code in order to determine what the attackers were hoping to accomplish.
“The attackers did not seem to have a good quality assurance process or perhaps the technical expertise to understand what will happen if they simply included an automatically generated CVE-2012-0158 exploit in combination with CVE-2017-0199,” said Cisco’s Vanja Svajcer.
In most attacks involving CVE-2017-0199, attackers send out specially crafted documents set up to exploit the vulnerability that exists in code responsible for handling OLE2Link embedded objects. By pointing a remote OLE2Link object to an HTML application file (HTA), the application will get executed and the malware is delivered.
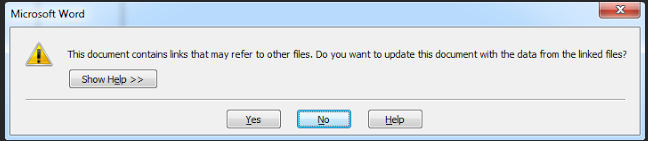
One problem with this attack is that Word informs the user that the document contains links which may refer to other files and asks them if they want to update the document. While exploitation takes place regardless of the user’s answer, the dialog could still raise suspicion.
In the attack exploiting both vulnerabilities, the initial document exploits CVE-2017-0199, but instead of an HTA file, the OLE2Link object points to another document exploiting CVE-2012-0158, which in turn fetches Ramnit and Lokibot.
Due to some mistakes made by the cybercriminals, Word crashes when loading the second exploit. However, had the exploit chain worked, the malware would have been downloaded without the “document contains links” dialog being displayed.
“One has to wonder why did the attackers use the combination of a newer and an older exploit at all? The combination would not be executed if the targeted system had a patch against either of the exploits. In addition, if the targeted system was vulnerable to CVE-2012-0158 it would be much easier for the attackers to use a single exploit targeting this vulnerability,” Svajcer explained.
“An assumption we can make is that that the attackers used the combination to avoid Word displaying the prompt which may raise suspicions for the target end user. Another possibility is that they attempted to use this combination in order to avoid behavioral detection systems which may be triggering on the combination of Ole2Link in a word document and a download of an HTA file,” the expert added.













