Owners of Ruckus access points (APs) have been warned that a DDoS botnet named AndoryuBot has been exploiting a recently patched vulnerability to hack devices.
The vulnerability in question is tracked as CVE-2023-25717 and it was patched by Ruckus in February in many of its wireless APs. The vulnerability allows a remote, unauthenticated attacker to execute arbitrary code and take complete control of a targeted Ruckus device.
Technical details have been available since February and cybersecurity firm Fortinet started seeing attacks exploiting the vulnerability in late April.
The company issued a warning on April 28 about CVE-2023-25717 being exploited, and on Monday it revealed that a spike in exploitation is driven by the AndoryuBot botnet.
AndoryuBot emerged in February 2023 and it’s designed to abuse compromised devices to launch various types of DDoS attacks.
The vulnerability is exploited to gain access to Ruckus APs. A script is then downloaded to the compromised device for propagation to other devices.
“Once a target device is compromised, AndoryuBot quickly spreads and begins communicating with its C2 server via the SOCKS protocol. In a very short time, it is updated with additional DDoS methods and awaits attack commands,” Fortinet explained.
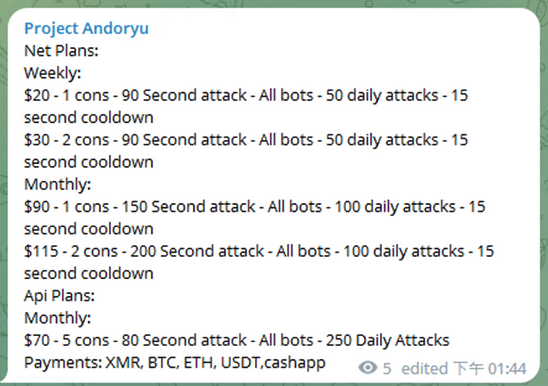
Prices for DDoS attacks using the AndoryuBot botnet are listed on a Telegram channel — threat actors can cause disruption even with limited financial resources.
Fortinet has made available indicators of compromise (IoCs) and other technical details that can be useful to defenders.
Fortinet’s warning comes just as the US Justice Department announced the seizure of 13 internet domains associated with DDoS-for-hire services. It also announced that four individuals charged last year for operating such services have pleaded guilty.
Related: Zerobot IoT Botnet Adds More Exploits, DDoS Capabilities
Related: Mirai Botnet Launched 2.5 Tbps DDoS Attack Against Minecraft Server
Related: Thousands Access Fake DDoS-for-Hire Websites Set Up by UK Police

