Norwegian metals and energy giant Norsk Hydro, one of the world’s biggest aluminum producers, has been hit by a ransomware attack that has impacted operations, forcing the company to resort to manual processes.
In a press conference on Tuesday, Norsk Hydro representatives revealed that the attack, which they described as extensive, started on Monday at around midnight, Norway time, when the company’s security team noticed some unusual activity on its global network. They said the ransomware is designed to encrypt files, but they have yet to determine exactly which malware family it belongs to.

Norway’s national CERT, NorCERT, reported that the attack was powered by a relatively new piece of ransomware named LockerGoga and that it may have also involved an attack on the company’s Active Directory system. NorCERT has warned other Norwegian companies about the attack.
LockerGoga is believed to have been used earlier this year in an attack aimed at French engineering consultancy Altran Technologies.
The Norwegian National Security Authority, whose representatives took part in the Norsk Hydro press conference, said the ransomware could be LockerGoga, but they are currently looking at several possible culprits.
MalwareHunterTeam researchers reported seeing a LockerGoga sample being uploaded to VirusTotal from Norway on Tuesday and they believe it’s “probably” the one used in the Hydro attack.
Adam Meyers, VP of Intelligence at CrowdStrike, also reported that a new sample of LockerGoga was recently uploaded to a public malware repository.
“While details of the Norsk Hydro incident are still developing, CrowdStrike Intelligence has been able to identify a new sample of the LockerGoga ransomware that was uploaded to a public malware repository in two ZIP files from an IP address based in Oslo, Norway,” Meyers said.
Norsk Hydro says it has recent backups that should help it restore encrypted files without the need to pay the ransom demanded by the attackers. The ransom amount has not been specified.
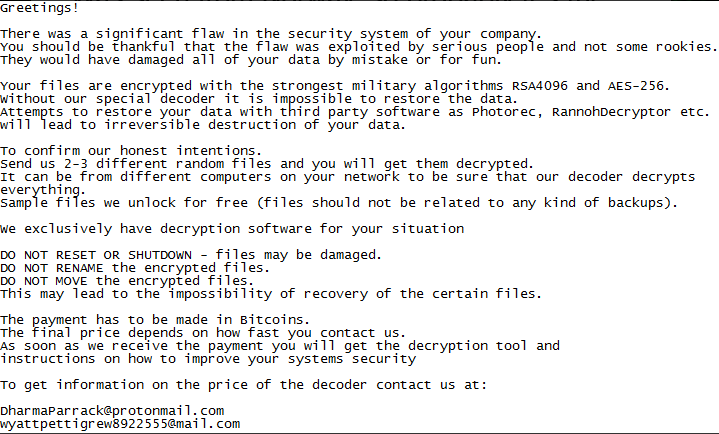
The ransom note typically dropped by LockerGoga does not specify any amount and instead instructs victims to contact the attackers via email for information on the price of the file decryption tool.
In the case of the Norsk Hydro attack, the ransomware has managed to spread to multiple plants and it has impacted operations in several “business areas.” However, the company says it has not led to safety-related incidents.
Norsk Hydro said production in its Energy and Bauxite & Alumina units is running normally, and no plants outside of Norway appear to have been hit. Plants within Norway are allegedly running normally, but they have been forced to rely to a high degree on manual processes. Some small plants did have to stop for a short period of time, the firm said.
“Lack of ability to connect to the production systems causing production challenges and temporary stoppage at several plants,” the company wrote in a statement posted on Facebook.
The company has been working to isolate plants in an effort to prevent the ransomware from spreading, and it’s now trying to identify the malware and finding a “cure.”
Norsk Hydro has been collaborating with external cybersecurity experts and the Norwegian National Security Authority to respond to the attack and investigate it.
The organization says losses are minimal at the moment, but they will likely increase depending on how long it takes to restore systems.
Destructive cyberattacks have been known to cost big companies hundreds of millions of dollars — a perfect example is the NotPetya attack launched in 2017.
Current customer orders are being managed using printouts and by adding more people to each shift, but some future orders may be impacted, depending on each plant. The aluminum giant said it used these types of manual processes several years ago, which helps it deal with this situation.
Norsk Hydro could not provide an estimate on how long it will take to restore all systems.
“Manufacturing companies are an obvious target for ransomware because downtime is measured in millions of dollars per day — so as you might expect, CEOs are eager to pay. Plus the security of industrial networks has been neglected for years, so malware spreads quickly from infected employee computers in a single office to manufacturing plants in all other countries,” Phil Neray, VP of Industrial Cybersecurity at CyberX, told SecurityWeek. “These attacks are especially serious for metal or chemical manufacturers because of the risk of serious safety and environmental incidents, and the bottom-line impact from spoilage of in-process materials and clean-up costs.”
The company’s shares are down roughly 2 percent at the time of writing and Reuters reported that news of the cyberattack resulted in a 1.2 percent increase in aluminum prices.
“This is the first time I can recall a cyberattack impacting the spot price of a global commodity like aluminum,” said Tod Beardsley, Research Director at Rapid7. “That alone is pretty significant, since it reminds us that cyber-exposure can have a real, direct effect on industries that aren’t normally thought of as ‘high tech’ industries. Today’s report of the Norsk Hydro outage is a reminder that all businesses and organizations, no matter their industry, vertical, or size, need to step up their game when it comes to information security fundamentals in our increasingly interconnected world.”
Related: Industrial Systems at Risk of WannaCry Ransomware Attacks
Related: ICS Security Pros Increasingly Concerned About Ransomware
Related: Cyberattack on German Steel Plant Caused Significant Damage
Related: Port of San Diego Hit by Ransomware













