Experts and vendors have warned that industrial control systems (ICS) are also at risk of being compromised in WannaCry ransomware attacks.
The WannaCry ransomware, also known as Wanna Decryptor, WanaCrypt0r, WannaCrypt, Wana Decrypt0r and WCry, has infected more than 200,000 systems worldwide, including ones housed by banks, hospitals, ISPs, government agencies, transportation companies and manufacturing plants.
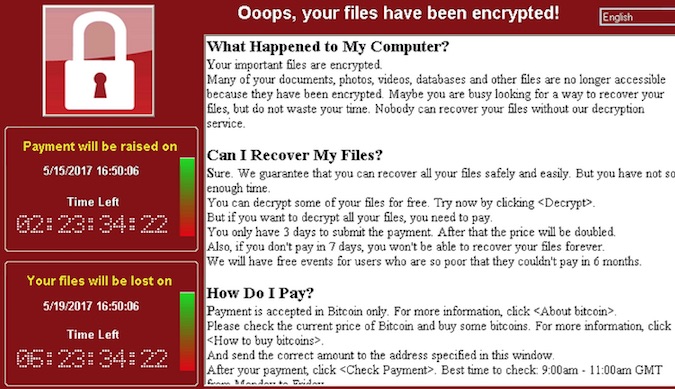
While the campaign has helped the attackers make more than $50,000 in just a few days, not everyone is convinced that profit-driven cybercriminals are behind the operation, with some suggesting that it could be the work of a nation-state actor.
The attacks involved an exploit named EternalBlue and a backdoor dubbed DoublePulsar, both leaked recently by a hacker group calling itself Shadow Brokers. The exploits were allegedly used by a threat actor called the Equation Group, which has been linked to the NSA.
The EternalBlue exploit leverages a Server Message Block (SMB) vulnerability in Windows that can be exploited remotely without user interaction, which is the main reason why the ransomware managed to wreak havoc.
The flaw was patched by Microsoft in March and the tech giant has even made available fixes for outdated versions of Windows. However, many organizations have not installed the patches and the situation is even more complicated in the case of industrial systems.
An advisory published by ICS-CERT on Monday informs users that automation giants Rockwell Automation and Schneider Electric have provided recommendations on how customers can prevent attacks. This includes installing Microsoft’s patches, updating security software, creating backups, training employees, and configuring access controls to block unauthorized access to sensitive systems.
ICS-CERT also referenced an advisory published by medical technology firm BD (Becton, Dickinson and Company), which issued a warning after the WannaCry attacks affected many healthcare facilities.
ICS security firm Claroty pointed out that the ransomware has already hit Windows systems running ICS software, causing failures that impacted production. Some of the affected manufacturing companies decided to halt production due to concerns for personal safety and potential damage to expensive assets.
The company believes industrial environments are particularly susceptible to these types of attacks for several reasons, including the improper segmentation of IT and OT networks, unpatched Windows machines, and the presence of SMB on devices hosting HMIs, engineering workstations, historians and other systems.
Another problem highlighted by Claroty is related to WannaCry’s kill switch. This kill switch involves a non-existent domain name that the malware contacts before initiating its malicious routine. If the domain does exist, the malware terminates – this has allowed the security community to neutralize some variants of the threat by registering the domain names specified in the malware code.
This discovery may have prevented many computers from becoming infected, but industrial systems are typically not connected to the public Internet, which makes the kill switch useless, Claroty said.
While patching Windows machines is the best way to prevent attacks, Barak Perelman, CEO of industrial cyber security company Indegy, noted that this is not an option in many industrial environments as these systems often need to operate non-stop and they cannot be restarted. Another problem is that deploying security patches could have a negative impact on the stability and availability of a system.
Phil Neray, VP of Industrial Cybersecurity at CyberX, also believes that patching the vulnerability is not easy in the case of ICS.
“It’s worth noting that many of the SCADA applications embedded in our electrical grid and manufacturing plants were developed years ago and are tethered to older versions of Windows — so the fix isn’t going to be easy,” Neray said.
“In the meantime, we should treat this attack as a persistent threat and continuously monitor both IT and OT networks for unusual activity. After all, how do we know that the same vulnerabilities haven’t already been well-exploited for cyber-reconnaissance and cyber-espionage purposes? Or, that this isn’t just the first phase of a more elaborate targeted campaign with the goal of causing massive disruption to our critical infrastructure and our economies?” the expert added.
Related: New SCADA Flaws Allow Ransomware, Other Attacks
Related: Cyberattacks Ease After Global Pushback, Putin Points Finger at U.S.
Related: Microsoft Warns Governments Against Exploit Stockpiling












