Hi, what are you looking for?
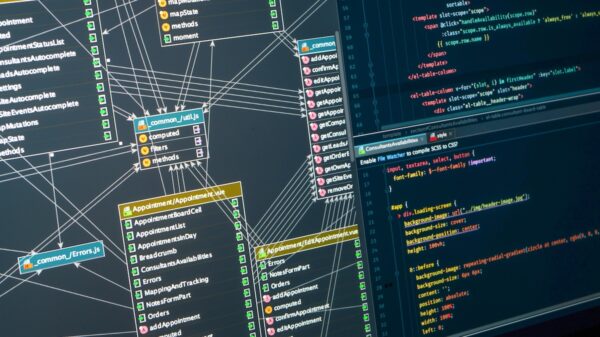
Network Security
Foreign attackers have many more toolsets at their disposal, so we need to make sure we’re selective about our modeling, preparation and how we...
Cybersecurity Funding
Risk and compliance solutions provider Sprinto has raised $20 million in a Series B funding round led by Accel.