Researchers at Arbor Networks’ Security Engineering and Response Team (ASERT) have identified what they believe to be a tool used in advanced persistent threat (APT) attacks aimed at various entities in East Asia.
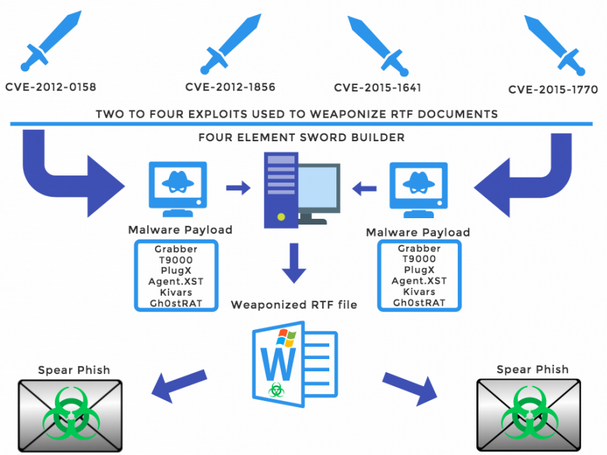
An analysis of a dozen incidents from a larger set of activity has led experts to believe that the malicious Rich Text File (RTF) documents used by threat actors in their attacks were all created using the same builder.
The attacks analyzed by ASERT were part of long-running APT campaigns aimed at the Tibetan community, journalists and human rights groups in Taiwan and Hong Kong, and Uyghurs. The operations involved pieces of malware known as Kivars, PlugX, Gh0stRAT, T9000, Graber and Agent.XST.
According to researchers, these threats were primarily delivered to victims via spear-phishing emails that contained a malicious RTF document with the .doc extension. Interestingly, these files were each set up to exploit 2-4 vulnerabilities and Arbor Networks believes they might have been created with a weaponized document builder which it has dubbed “Four Element Sword.”
The Four Element Sword builder is capable of embedding code for four different Microsoft Office arbitrary code execution exploits. Two of the flaws, CVE-2012-0158 and CVE-2012-1856, were first discovered in 2010 and patched by Microsoft in 2012, while the other two, CVE-2015-1641 and CVE-2015-1770, were resolved last year. While some of these exploits are very old, researchers believe they could still be useful against certain groups that might be using older systems.
For each of the 12 attacks it analyzed, Arbor Networks made connections to malware and infrastructure observed in other attacks — most notably a campaign aimed at the World Uyghur Congress and an operation dubbed by Trend Micro “Shrouded Crossbow.”
The types of targets, the pieces of malware used, overlaps in infrastructure and connections to previous campaigns suggest a link to China. ASERT has found evidence that the campaigns leveraging malicious RTF documents are ongoing.
According to researchers, the Four Element Sword builder has also been used by cybercriminals. In the cybercrime operations observed by the security firm, which will be detailed in an upcoming report, 2-3 of the Office exploits were integrated in each document.
Coinciding with ASERT’s report, the University of Toronto’s Citizen Lab disclosed the details of a cyber espionage campaign targeting Hong Kong democracy activists. The operation described by Citizen Lab is related to the threat activity detailed by ASERT.
















