A digital certificate stolen from Sony Pictures under the recent high-profile cyber attack has been used to sign malware, according to a report from Kaspersky Lab.
Ironically, the malware sample found digitally signed by the legitimate certificate from Sony was a sample of “Destover”, the destructive malware family that was reportedly used against Sony in the recent attack that resulted in troves of stolen corporate and personal data being leaked, along with the destruction data on corporate PCs.
Sony’s digital certificates, which were leaked by the attackers could be used to sign other malware samples and used in other attacks, but in this case it may not have been actually used by someone with malicious intent.
However, CSO’s Steve Regan has pointed out that the malware sample, which was uploaded to Malwr, was a joke between researchers.
The distrubting part, as Ragan reminded, is that after knowing its digital certificates had been obtained by attackers, Sony had not yet successfully revoked the known stolen certificates.
So while this incident may be a joke, the risk of Sony’s certificates being used in malware for real attacks is a reality.
 “Because the Sony digital certificates are trusted by security solutions, this makes attacks more effective,” Kaspersky Labs’ Global Research & Analysis Team wrote in a blog post. “We’ve seen attackers leverage trusted certificates in the past, as a means of bypassing whitelisting software and default-deny policies.”
“Because the Sony digital certificates are trusted by security solutions, this makes attacks more effective,” Kaspersky Labs’ Global Research & Analysis Team wrote in a blog post. “We’ve seen attackers leverage trusted certificates in the past, as a means of bypassing whitelisting software and default-deny policies.”
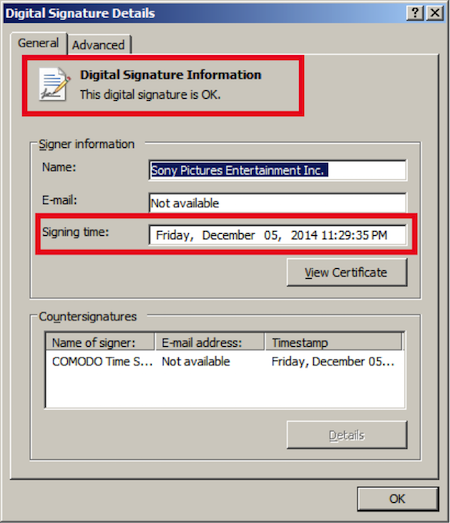
According to Kaspersky Lab, it appears as though the new sample was signed on December 5, 2014 and it virtually the same as a previously observed non-signed file.
Kaspersky said that stolen digital certificate was reported to COMODO and Digicert, which should be blacklisted shortly.
“As more news on the Sony Pictures Entertainment breach trickles out, it’s not surprising to learn that the new version of the Destover malware used by the attackers was signed by a legitimate certificate from Sony,” Kevin Bocek, VP of Security Strategy and Threat Intelligence at Venafi, told SecurityWeek. “Time and again, we’re seeing breached organizations like Sony leave open doors for attackers by failing to protect the trust provided by digital certificates and cryptographic keys.”
“Bad actors have learned that the easiest, fastest and most effective way to inject malware that resides undetected on corporate networks is by signing the malware with compromised or stolen digital certificates,” Bocek continued. “Attackers know that most organizations cannot detect or respond to anomalous certificates that authenticate systems and users on their networks, devices and applications, so they exploit them, just as they did in the Sony hack.”
“Global companies typically have tens of thousands of keys and certificates and the majority do not take an accurate inventory of them, do not know where they are deployed, who is using them and do not have the right systems in place to secure them.”
“As noted by Kaspersky, these stolen Sony certificates are the exact opening attackers need and can lead to further, more detrimental attacks,” Bocek said. “SSL and SSH cloaks an attacker’s communication channel and makes it nearly invisible – this is exactly what they’re looking for to carry out their cyber crimes.”
*Updated with additional information on sample thought to be a joke between researchers.
















