With the rise in complex threats and new advanced malware flooding headlines and causing a stir, it’s easy to forget about some of the sizable threats that have graced the security word over the years—threats that may be out of mind, but shouldn’t be.
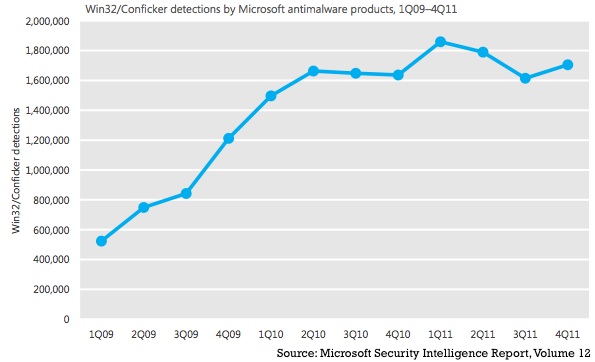
In its Security Intelligence Report volume 12 (SIRv12), which was released today, Microsoft said the Conficker worm was detected approximately 220 million times worldwide in the past two and a half years. More concerning, is that by Microsoft’s numbers, quarterly detections of the Conficker worm have actually increased by more than 225 percent since the start of 2009. In the fourth quarter of 2011 alone, Conficker was detected on 1.7 million systems worldwide, Microsoft said.
Why is Conficker’s still so prevalent in organizations? Microsoft cites research that shows 92 percent of Conficker infections were a result of weak or stolen passwords, and 8 percent of infections exploited vulnerabilities for which a security update exists.
Just a year ago, SecurityWeek columnist Ram Mohan brought the matter to attention, suggesting that (at the time) two years after the conficker worm appeared, we are still at risk.
As Mohan explained in his column, “Conficker emerged in late November 2008, about a month after Microsoft pushed out an emergency patch for a critical vulnerability in Windows. Exploiting this vulnerability, the worm quickly spread to unpatched computers around the world, and one month later was followed up with a “B” variant.”
“Conficker is one of the biggest security problems we face, yet it is well within our power to defend against,” said Tim Rains, director of Microsoft Trustworthy Computing. “It is critically important that organizations focus on the security fundamentals to help protect against the most common threats.”
“What most worried the security industry were Conficker’s update mechanisms,” Mohan explains. “The malware was designed to go out onto the Internet every day and update itself by connecting over the Web to any one of 250 randomly generated domain names in eight top-level domains (TLDs) – .com, .org, .info, .net, .cc, .biz, .cn and .ws. Each day, the list of domains would be generated using the date as a seed. This meant that the attacker needed to spend only a few dollars to register one domain and upload his encrypted update to a Web server to patch Conficker with the code of his choice. The potential for mischief was huge. Conficker could potentially have been used to spread further malware, conduct infrastructure-threatening denial of service attacks, or carry out essentially whatever nefarious activity the controller desired.”
“Labeling cyberthreats as ‘advanced’ is often times misleading and can divert organizations’ attention away from addressing basic security issues, which can prevent more common threats from infiltrating their systems,” Rains said. “Most attacks do not possess new, super-advanced techniques or technology as the APT label implies; in the majority of cases, they simply exploit weak or stolen passwords or vulnerabilities for which a security update exists and employ social engineering.”
For advice, Microsoft recommends that customers and businesses adhere to the following security fundamentals to help ensure they are protected:
• Use strong passwords and educate employees on their importance
• Keep systems up to date by regularly applying available updates for all products
• Use antivirus software from a trusted source
• Invest in newer products with a higher quality of software protection
• Consider the cloud as a business resource
While it’s important to keep an eye out for new threats, it’s also important to not forget about threats of the past.
The latest Microsoft Security Intelligence Report, which provides insight into online threat data with new information for July 2011 through December 2011 and analysis of data from more than 100 countries and regions around the world is available as a PDF download here.
















