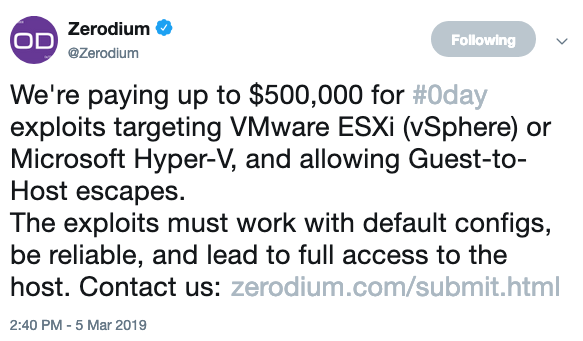
Exploit acquisition firm Zerodium this week announced that it’s prepared to pay up to $500,000 for VMware ESXi and Microsoft Hyper-V vulnerabilities.
The company says it’s looking for ESXi (vSphere) and Hyper-V exploits that allow guest-to-host escapes. The exploits need to work on default configurations, they must be reliable, and they have to allow the attacker to gain full access to the host.
Until now, Zerodium has been offering up to $200,000 for ESXi virtual machine escapes — the payout was increased earlier this year from $100,000.
“We are increasing the payouts for VMWare ESXi exploits to attract and encourage more researchers into auditing the security of this hypervisor as we firmly believe that there are many critical vulnerabilities affecting it and our government customers are in need of such exploits,” Chaouki Bekrar, founder and CEO of Zerodium, told SecurityWeek.
Microsoft Hyper-V was not part of the company’s bug bounty program until now.
“Hyper-V was not part of our bounty program as there was low to no interest in this product from our customers,” Bekrar explained. “However, we’ve recently observed a significant increase in demand for Hyper-V exploits and we have decided to add it to our program.”
It’s worth noting that Microsoft offers up to $250,000 for Hyper-V vulnerabilities through its bug bounty program.
Bekrar says Zerodium will offer up to $500,000 for Hyper-V and ESXi zero-day exploits for a couple of months and then it will decide if the payouts will be reduced or kept at this level depending on the number of submissions received from researchers.
Zerodium offers up to $2 million for high-quality exploits. The company says the information it acquires is provided to customers, which it claims are mainly government organizations “in need of specific and tailored cybersecurity capabilities and/or protective solutions to defend against zero-day attacks.”
Earlier this year, Zerodium announced that it’s prepared to pay up to $2 million for remote iOS jailbreaks and $1 million for vulnerabilities in popular chat applications, including WhatsApp, iMessage and SMS/MMS apps.
Related: Zerodium Discloses Flaw That Allows Code Execution in Tor Browser
Related: Zerodium Offers $45,000 for Linux 0-Days
Related: Zerodium Offers $500,000 For Messaging, Email App Exploits












