YARA 4.0.0 was released on Wednesday with some important new features and performance improvements.
YARA is a highly popular open source tool designed to help researchers identify and classify malware samples. It has been described as “the pattern-matching swiss knife for malware researchers.”
The previous update to YARA, version 3.11.0, was released in October 2019, but Victor Alvarez, the creator of YARA, who currently works as a software engineer for Google’s VirusTotal service, on April 29 announced the release of version 4.0.0.
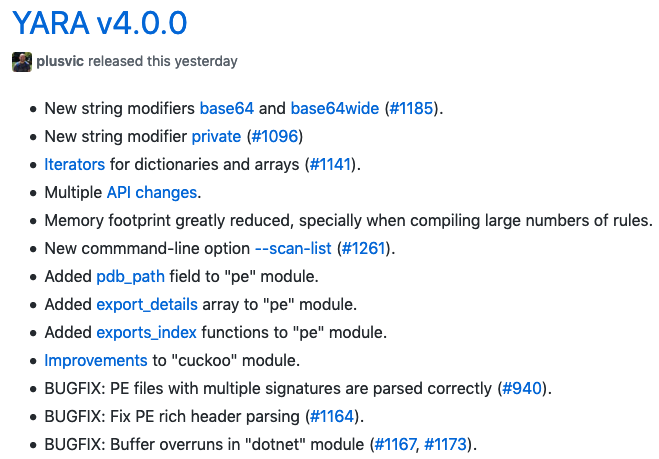
The latest major release of YARA includes new string modifiers, API changes, a reduced memory footprint, improvements to the PE and Cuckoo modules, and various bug fixes.
Kaspersky’s Costin Raiu, who is an expert on YARA and who on Wednesday hosted a short workshop on using Yara at Kaspersky’s SAS@home virtual event, said YARA 4 brings a few new features that researchers have been hoping to see for some time.
“The base64 string modifier is super useful and I’m sure it will see a lot of use in practice,” Raiu told SecurityWeek. “Similarly, the pdb_path in the ‘pe’ module is a much welcomed feature, that allows for fine tuning detections and potentially opening the door for some new ideas on how to catch malware. Changes and bugfixes aside, the memory footprint usage is possibly the top improvement; in the end, performance is super important for most users.”
YARA has been highly useful to many cybersecurity companies and researchers, often helping them identify zero-day exploits, new malware, and interesting links.
Related: Kaspersky Open Sources Internal Distributed YARA Scanner
Related: New Version of Infection Monkey Maps to MITRE ATT&CK Framework
Related: Cisco Releases Open Source Malware Signature Generator
Related: Open Source Tool From FireEye Automates Analysis of Flash Files

