Normally you wouldn’t think something as mundane as farming equipment could incite a lot of cyber malice, right? But that’s exactly what happened. I’ve recently run into a spate of DDoS attacks against farming equipment manufacturers and resellers. The attacks are dispersed enough in time to conclude that they are not part of a coordinated campaign. In fact, in each case the attackers appear to be known (or at least suspected) and their motives are clear and distinct from each other. Eventually, I got the back-story for three of these attacks and figured it would be illuminating to share.
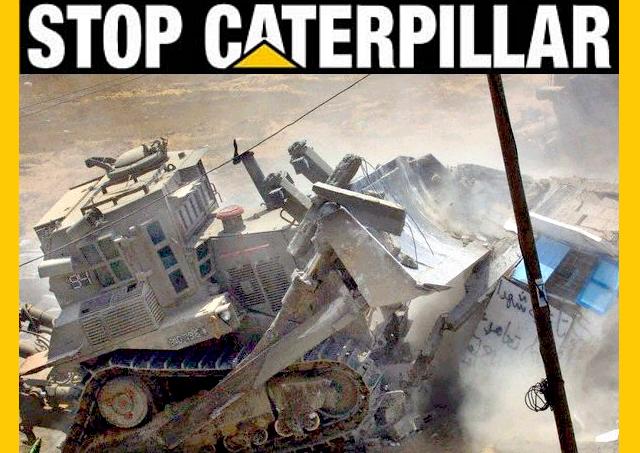
Weaponized Bulldozers
Bulldozers and other earth-moving devices are used for all kinds of work besides agriculture. In the conflict between the Israelis and the Palestinians, the former have been accused of bulldozing the housing projects of the latter. The occupants of the housing retaliated by hurling bricks and other objects at the bulldozer operators. The former then purchased and deployed weaponized bulldozers. These bulldozers were armored; some of them were even rumored to have anti-personnel ordinance mounted to the sides. All it took was someone to tweet a picture of the weaponized bulldozer clearly displaying the manufacturer logo, and cyber activists launched a DDoS attack against the bulldozer’s American manufacturer which, of course, had no impact on the land-clearing project.
Global Warming?
The perceived victims in this second story are trees. An American manufacturer of agricultural and forestry equipment has faced DDoS attacks for another political reason. The forestry equipment has seen heavy use in the Pacific Northwest forests of Canada and the United States. Anti-logging activists in the area—who once would have protested by getting in front of the machines in cold rain in the forest—have now found it easier to launch DDoS attacks against the manufacturer of the equipment.
Unfriendly Competition
Another series of DDoS attacks occurred in a state capital in the heartland of America. Farms surround the city for hundreds of miles in every direction, so there is a heavy base of agricultural manufacturers and resellers. A local auction website specialized in used farming equipment; when famers were done with their bulldozer, tractor, or combine, they would put it up for auction at the website. A competing local auctioneer got the idea to place a bid and then DDoS the site until the auction was over. Auction sites of any kind are natural targets for DDoS attacks. Everyone who participates would like his or her bid to be the last, and therefore winning, bid. One way to ensure a win is to place a bid and then DDoS the website, preventing anyone else from placing a bid.
In the first two cases, little could be done by involved parties other than to reinforce cyber defenses and implement countermeasures. In the case of the auction site, however, the attackers were very likely U.S. citizens attacking a U.S. company. As a result, criminal laws apply, and the attackers, if they are ever identified, could face significant jail time (up to 15 years).
The meta for all of these DDoS stories is that political and financial pressures continue to be the top motivations for cyber-attacks. Nearly any company can find itself in the crosshairs of political activists or someone looking to make a quick buck. Companies that you would not expect to be making these kinds of headlines could find themselves at the center of the next story.
Related: Download the DDoS Response Playbook
Related: Top 10 DDoS Attack Trends















