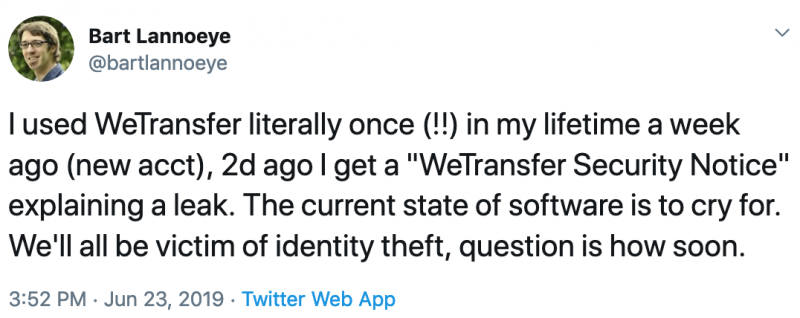
The popular file transfer service WeTransfer issued a security notice on Friday after discovering that some file transfer emails were sent to the wrong individuals.
According to WeTransfer, file transfer emails were sent to unintended email addresses on June 16 and 17. After the incident was discovered, some users have been logged out of their account and instructed to reset their password. In addition, the company said it blocked the impacted transfer links.
“We have learned that a transfer you sent or received was also delivered to some people it was not meant to go to. Our records show that those files have been accessed, but almost certainly by the intended recipient. Nevertheless, as a precaution we blocked the link to prevent further downloads,” WeTransfer said in an email sent to impacted users.
WeTransfer warned affected individuals to keep an eye out for any “suspicious or unusual emails.”
SecurityWeek has reached out to WeTransfer to find out what caused the incident and how many users are impacted. This article will be updated if the company responds.
At least one security expert speculated that WeTransfer may have been hacked.
Related: Flipboard Resets User Passwords in Response to Data Breach
Related: Google Warns G Suite Customers of Passwords Stored Unhashed Since 2005












