The US Treasury Department on Tuesday announced sanctions against two ‘cybersecurity experts’ accused of running a platform affiliated with the Islamic State group.
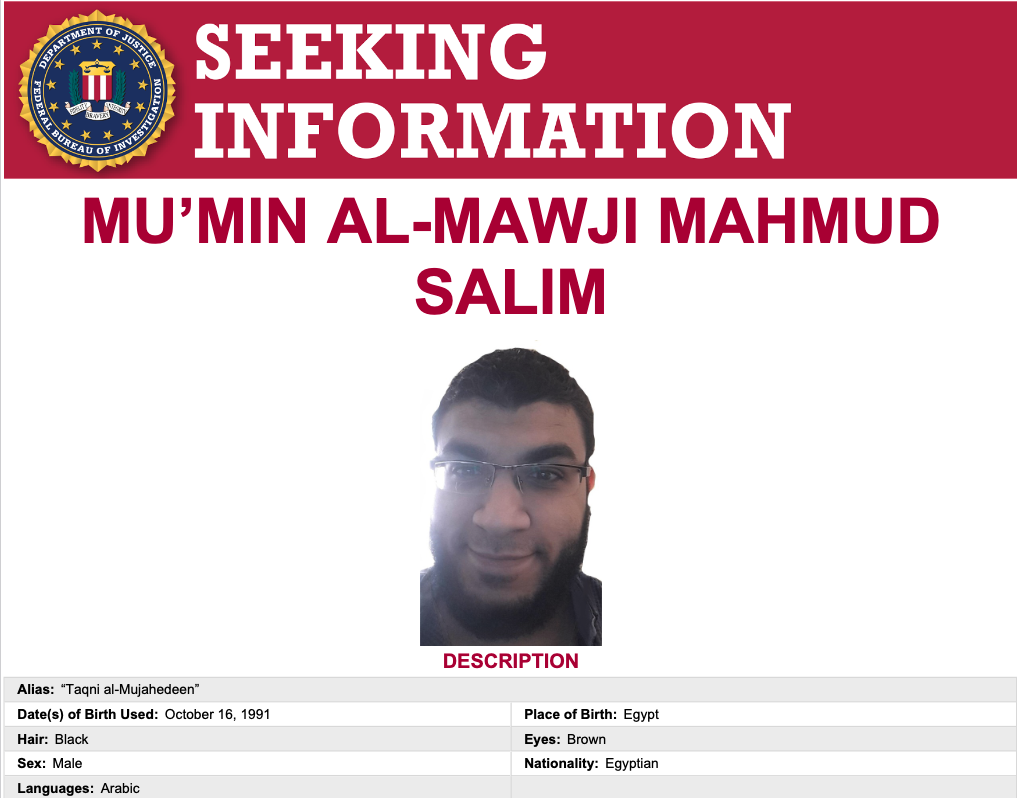
The sanctioned individuals are both Egyptian nationals. One of them is Mu’min Al-Mawji Mahmud Salim, the creator of a platform named Electronic Horizons Foundation (EHF), which provides cybersecurity training and guidance to ISIS supporters.
The platform offers information on conducting cyber operations, including for evading law enforcement and working with cryptocurrencies.
The second sanctioned individual is Mu’min Al-Mawji’s partner, Sarah Jamal Muhammad Al-Sayyid, who allegedly helped run the EHF platform.
“Sarah Jamal recruited other ISIS members to join EHF and procured web servers to host ISIS platforms on behalf of EHF. Sarah Jamal collaborated with Mu’min Al-Mawji on EHF projects including logistical management and cryptocurrency support,” the Treasury Department said.
The two have been added to the FBI’s wanted list and the agency is offering rewards of up to $20,000 for information on their location.
The latest round of sanctions also targeted Faruk Guzel, a Turkish national accused of transferring funds to ISIS-affiliated individuals in Syria.
The sanctions come roughly one week after the US, UK and Australia announced sanctions against a Russian man for his role in the 2022 ransomware attack on Australian healthcare insurer Medibank.
Last year, the US sanctioned a North Korean university believed to be responsible for training the country’s hackers.
Related: US Sanctions North Korean Cyberespionage Group Kimsuky
Related: US Sanctions Cryptocurrency Mixer Sinbad for Aiding North Korean Hackers
Related: US Sanctions Russian National for Helping Ransomware Groups Launder Money

