Data Must be Protected as it Exists at All Points in the Processing Lifecycle
Data is often an organization’s largest and most valuable asset, making it a prime target for all types of adversaries both criminal and nation-state. Nearly every week a new data breach is announced, serving as a consistent reminder that data security matters. In the first half of 2018 alone, 944 breaches led to 3.3 billion data records being compromised. But what does true data security look like? Numerous solutions herald the necessity of and their ability to provide ‘end-to-end protection’ but when we break through the buzzwords, do we have a clear picture of what it means to secure data?
With attack vectors emerging from every possible angle and attackers becoming increasingly sophisticated, it has become clear that every part of data security matters — from secure data storage, transit, and processing to access control and effective key management. If one aspect is vulnerable, it undermines the effectiveness of the other security measures that have been put in place.
This multi-dimensional risk requires a holistic, data-centric approach to security, one focused on protecting the data itself at all points in its lifecycle rather than concentrating efforts only on its perimeter of surrounding networks, applications, or servers. Organizations must ensure data is secured at all times by:
1. Securing Data at Rest on the file system, database, or storage technology
2. Securing Data in Transit as it moves through the network
3. Securing Data in Use, while the data is being used or processed
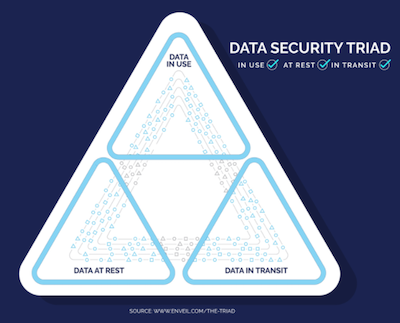
Together, these elements form the Data Security Triad, representing the trifecta of protection required to ensure data is secure throughout its entire lifecycle.
At the core of this protection strategy is encryption. Encryption renders data useless to an attacker, making it unreadable and therefore removing its value. Thus, encryption is able to undermine the attackers’ purpose – stealing assets of value – and makes the target infinitely less appealing.
Experience tells us that if there is data of value at stake, attackers will find a way to find and reach it – we can’t just lock the front door; every point of entry needs to be protected. Consequently, limiting encryption to only a portion of the Data Security Triad is a dangerous oversight. It is critical to protect data at rest, in transit, and in use.
• Data at Rest: Inactive data stored in any digital form, Data at Rest may be located on the hard drive or in databases, data lakes, cloud storage, or countless other locations. Often thought of as the safest state of data, we typically see perimeter-based technologies and solutions implemented as a first line of defense, with additional layers added depending on the purpose and sensitivity of the data itself. These extra measures include keeping sensitive data encrypted whether stored on premise or in the cloud. Due to the aggregated nature of data storage, Data at Rest is an attractive target for attackers interested in exfiltrating large quantities of valuable data.
• Data in Transit: Data is vulnerable while in transit, whether moving through a private network, local devices, or a public/untrusted space. It is widely recognized that encrypting Data in Transit is standard practice – it’s typically one of the first areas of focus for a security team as they look to lock down data assets. It’s a must have – and as long as businesses adhere to proper protocols, transport encryption is an efficient and effective line of defense.
• Data in Use: If the two previously described states of data can be simplistically labeled as the best understood and most solutioned, Data in Use should be referred to as most overlooked. As such, it has quickly become the point of least resistance for an attacker. At the most basic level, the challenge in the Data in Use arena is tied to a lack of recognition of the problem itself. The vulnerability has been ignored in part because some in the security world incorrectly assume that protecting Data at Rest and Data in Transit means their work is done. However, the increasing sophistication of attackers coupled with the foundation-rattling disclosures regarding flaws in the processing mechanisms of ubiquitous computer chips requires that businesses of all sizes open their eyes to the importance of protecting Data in Use. Data is most valuable when we’re using it to extract insights, which can be accomplished by executing searches or analytics to deliver critical information. Beyond access controls and user authentication, which are important parts of any security plan, there are a variety of commercially available solutions and technical methods being used to combat this vulnerability including homomorphic encryption, secure multiparty compute, and secure enclave technologies.
We know attackers are evolving and our security practices must evolve as well. Protection schemes must recognize and secure data as it exists at all points in the processing lifecycle, whether at rest, in transit, or in use.













