Security researchers at Recorded Future have spotted a suspected Chinese APT actor targeting a wide range of critical infrastructure targets in India, including power plants, electricity distribution centers and Indian seaports.
Recorded Future, a threat-intelligence firm based in Somerville, Mass., said the wave of targeted attacks appear to coincide with the ongoing territorial conflict between India and China.
The company’s analysts applied the “RedEcho” moniker to this threat actor and warned that the group has strong infrastructure and victim overlaps with the notorious APT41/Barium actor.
Despite these overlaps with known APT actors, Recorded Future said it will contrinue to track the group as a distinct actor because there isn’t enough evidence to firmly attribute the activity to a singular group.
[ Learn more about threats to industrial systems at SecurityWeek’s ICS Cyber Security Conference and SecurityWeek’s Security Summits virtual event series ]
From about the middle of 2020 onwards, Recorded Future said it captured telemetry showing a steep rise in the use of known APT command-and-control servers “to target a large swathe of India’s power sector.”
A detailed technical report from Recorded Future said 10 distinct Indian power sector organizations were targeted, including 4 of the 5 Regional Load Despatch Centres (RLDC) responsible for operation of the power grid. Other targets identified included two unidentified Indian seaports.
The company’s threat hunters identified 21 IP addresses among the list of targets in India, noting that they all qualify as critical infrastructure in India.
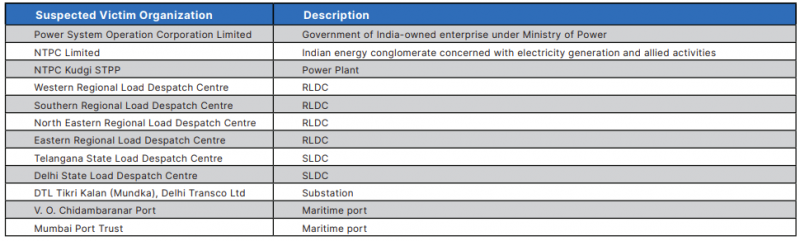
The researchers also noticed the targeting of a high-voltage transmission substation and a coal-fired thermal power plant.
“The targeting of these critical power assets offer limited economic espionage opportunities, but pose significant concerns over potential pre-positioning of network access to support other Chinese strategic objectives,” the company added.
Recorded Future has released IOCs and mitigation guidance to help organizations look for signs of malicious activity on corporate networks.
Related: Remote Hacker Caught Poisoning Florida City Water Supply
Related: U.S. Gov Warning on Water Supply Hack: Get Rid of Windows 7












