Cybersecurity firm ESET on Tuesday published a report detailing what it described as a previously undocumented piece of malware that had been observed targeting high-performance computing (HPC) clusters.
ESET has named this piece of malware Kobalos due to its small size (x86-64 samples are only 25 Kb) and its many tricks — Kobalos is a mischievous creature from Greek mythology. While the company’s analysis focuses on the Linux version of the malware, researchers say Kobalos also works on FreeBSD and Solaris, and possibly on Windows and AIX systems as well.
ESET says it hasn’t been able to determine the goals of the Kobalos operators, particularly since it could only obtain the malware itself and not any network traffic generated by an attack. However, the company hopes that its report could help others further analyze the threat.
The first known victim of Kobalos was spotted in late 2019 and ESET said the group operating the malware had remained active throughout 2020. However, the analyzed code also contained strings related to very old Microsoft operating systems, specifically Windows 3.11 and Windows 95.
Threat actors targeting supercomputers — often for cryptocurrency mining — is not unheard of, but the cybersecurity company’s researchers have not found any links between Kobalos and previously reported incidents. Kobalos has not been seen attempting to abuse compromised supercomputers for cryptocurrency mining.
Moreover, Kobalos has been observed targeting other types of entities as well. ESET says victims include an endpoint security solutions provider, government agencies, and personal servers in North America; universities, HPC infrastructure, a marketing agency, and hosting firms in Europe; and a major ISP in Asia.
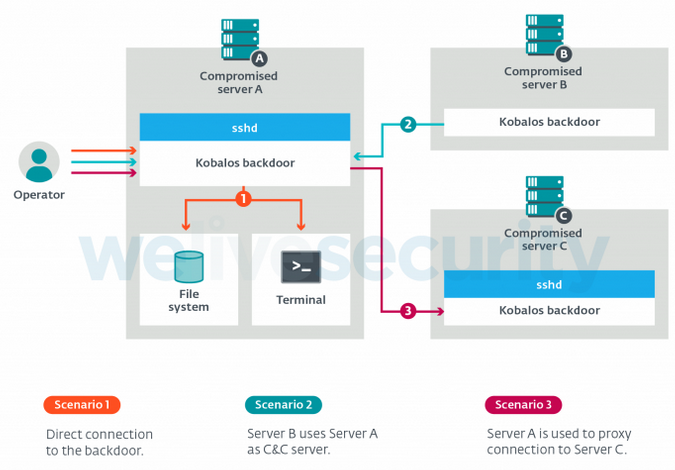
Researchers have described Kobalos as a “generic backdoor” that can allow its operators to perform a wide range of tasks, including gain remote access to the compromised device’s file system, spawn a shell and execute arbitrary commands, and use the infected device as a proxy. Kobalos stands out for having the C&C code within itself, which allows its operators to turn any compromised server into a C&C.
According to ESET, the attackers have also delivered a tool designed to steal credentials from SSH clients on devices infected with Kobalos — this stealer is actually a trojanized OpenSSH client. Researchers believe the threat actors may be using the stolen SSH credentials to help Kobalos spread to other servers.
“The numerous well-implemented features and the network evasion techniques show the attackers behind Kobalos are much more knowledgeable than the typical malware author targeting Linux and other non-Windows systems,” ESET said in its report. “Their targets, being quite high profile, also show that the objective of the Kobalos operators isn’t to compromise as many systems as possible. Its small footprint and network evasion techniques may explain why it went undetected until we approached victims with the results of our internet-wide scan.”
Related: Kinsing Linux Malware Deploys Crypto-Miner in Container Environments
Related: New ‘FreakOut’ Malware Ensnares Linux Devices Into Botnet















