Medtronic and the US government have warned that some Medtronic MiniMed insulin pumps are vulnerable to hacker attacks that can have serious consequences for their thousands of users.
Advisories have been published by the Department of Homeland Security (DHS) and Medtronic, and the Food and Drug Administration (FDA) has issued a press release to warn the public about a high-severity flaw affecting MiniMed 508 and Paradigm series insulin pumps.
The vulnerability, classified as an improper access control issue and tracked as CVE-2019-10964, was identified by Medtronic based on earlier research conducted by Nathanael Paul, Jay Radcliffe and Barnaby Jack, and more recent findings from experts Billy Rios, Jonathan Butts and Jesse Young.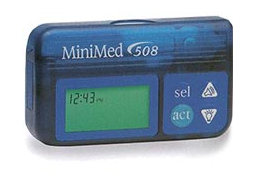
The flaw exists due to the fact that the impacted devices communicate with blood glucose meters, the remote controller and CareLink USB devices using a wireless RF protocol that does not properly implement authorization and authentication. An attacker who can intercept these communications can inject, replay or modify data, allowing them to change the device’s settings and control the delivery of insulin.
“The vulnerability allows a potential attacker with special technical skills and equipment to potentially send radiofrequency (RF) signals to a nearby insulin pump to change settings, impacting insulin delivery. This change could result in a patient experiencing hypoglycemia (if additional insulin is delivered) or hyperglycemia (if not enough insulin is delivered),” Medtronic warned.
The FDA says Medtronic has identified 4,000 patients in the United States that rely on the vulnerable pumps.
Medtronic’s advisory says the company is not aware of any instances where this vulnerability has been exploited and it recommends that patients and physicians continue using the devices. However, the company has advised patients in the United States to speak to their healthcare provider about replacing the device with a newer model that has better cybersecurity protections, such as the MiniMed 670G.
For individuals living outside the US and in countries where a newer pump model is not available, the vendor has advised customers to take precautions for preventing cyberattacks.
“Medtronic is unable to adequately update the MiniMed 508 and Paradigm insulin pumps with any software or patch to address the devices’ vulnerabilities,” the FDA noted.
The FDA press release says the affected insulin pumps are being “recalled,” but Medtronic representatives clarified for SecurityWeek that impacted devices are not required to be returned as the term “recall” has a different meaning in the medical device industry.
“In the medical device industry, the term ‘recall’ is used generally to cover a range of actions including, for example, customer or patient communications with additional instructions for use of the product or requests to return potentially impacted product,” Medtronic clarified.
Related: DHS Warns of Vulnerabilities in Medtronic Defibrillators

