SolarWinds has released a second hotfix for its Orion platform in response to the recent breach, and the company has decided to remove from its website a page listing some of its important customers.
IT management and monitoring solutions provider SolarWinds revealed this week that sophisticated threat actors compromised the build system for its Orion monitoring platform, which allowed the attackers to deliver trojanized updates to the firm’s customers between March and June 2020. The hackers could then compromise the servers of the organizations that downloaded, implemented or updated Orion products in that timeframe.
Shortly after news of the breach broke, the company informed customers about the availability of a hotfix, but promised to release a second hotfix that replaces the compromised component and provides additional security enhancements.
The company released that second patch on Tuesday, namely version 2020.2.1 HF 2 of the Orion platform, and it has informed customers that no other products have been compromised. The company has provided a complete list of both affected and not affected products, and it has published an FAQ document to answer some of the questions customers might have.
In an SEC filing this week, SolarWinds said it notified 33,000 customers about the incident, but pointed out that only up to 18,000 actually obtained the compromised software.
The attack is believed to have impacted many major organizations, including cybersecurity firm FireEye, which broke the news after the attackers stole some of its Red Team tools, and various U.S. government organizations.
According to media reports, the list of U.S. government targets could include the DHS, the Commerce Department, the Treasury, the Defense Department, the State Department, and the National Institutes of Health. Britain’s National Cyber Security Centre (NCSC) says it’s assessing the impact on the UK.
Related: Group Behind SolarWinds Hack Bypassed MFA to Access Emails at US Think Tank
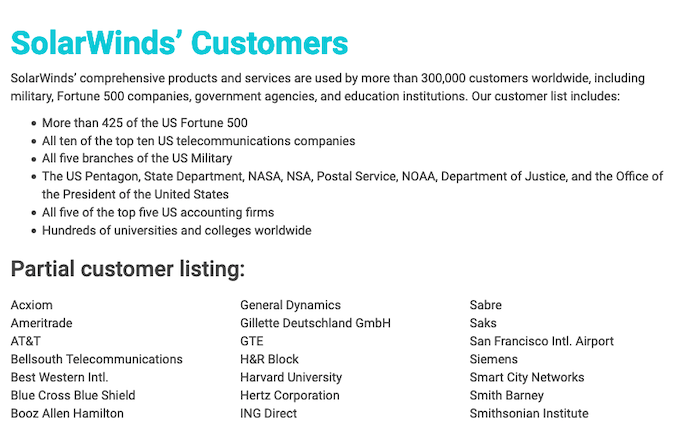
At around the time it released the second hotfix, SolarWinds decided to remove from its website a page listing high-profile customers. The now-removed page said the company had 300,000 customers worldwide, including 425 of US Fortune 500 companies, the top US telecoms and accounting firms, hundreds of universities and colleges, as well as several US government organizations.
Microsoft, which dubbed the attack Solorigate, has also taken steps to protect customers, including through updates for Microsoft Defender Antivirus that should ensure known malicious SolarWinds binaries are blocked.
While it’s still unclear exactly how the attackers managed to breach SolarWinds’ systems, some reports that emerged over the past days revealed security lapses. Reuters learned that multiple threat actors have offered to sell access to SolarWinds systems on underground forums. And one researcher said he informed SolarWinds in November 2019 that FTP credentials belonging to the company had been exposed in a public GitHub repository.
Russia appears to be the prime suspect for the SolarWinds hack, specifically the group tracked as APT29 and Cozy Bear, but the Kremlin has denied the allegations.
Related: Industry Reactions to FireEye Breach: Feedback Friday













