Tampered Versions of SolarWinds Orion IT Monitoring Software Used to Compromise Global Organizations
Incident response teams are scrambling as after details emerged late Sunday of a sophisticated espionage campaign leveraging a software supply chain attack that allowed hackers to compromise numerous public and private organizations around the world.
Among victims are multiple US government agencies, including the Treasury and Commerce departments, and cybersecurity giant FireEye, which stunned the industry last week when it revealed that attackers gained access to its Red Team tools.
FireEye indirectly confirmed the connection between the attack targeting its own systems, which it has blamed on an unidentified state-sponsored threat actor, and the attacks on U.S. government systems. The connection was made through a blog post published on Sunday, where FireEye described a widespread attack campaign that is exploiting SolarWinds’ Orion IT monitoring software.
According to the cybersecurity firm, the campaign started as early as the spring of 2020 and is ongoing.
FireEye said the attackers, which it tracks as UNC2452, have leveraged trojanized Orion updates in an effort to deliver a backdoor identified by the company as SUNBURST. In at least one case, the hackers also delivered a previously unknown memory-only dropper named TEARDROP, which in turn attempted to deploy a custom version of Cobalt Strike’s Beacon payload.
FireEye said it observed multiple victims, including government, technology, consulting, extractive and telecom organizations in North America, Europe, the Middle East and Asia. The company has notified victims and it has made available indicators of compromise (IoC) to help organizations detect potential attacks and conduct investigations.
The wide range of victims is not surprising considering that SolarWinds claims on its website that it has more than 300,000 customers worldwide. The software maker says its customers include over 425 of U.S. Fortune 500 firms, the top ten telecoms companies in the United States, the U.S. Military, the Pentagon, the State Department, the NSA, and the Department of Justice.
FireEye says the trojanized update file is a “standard Windows Installer Patch file that includes compressed resources associated with the update, including the trojanized SolarWinds.Orion.Core.BusinessLayer.dll component.”
A quick search on VirusTotal conducted by SecurityWeek early Monday revealed that the malicious file (MD5: b91ce2fa41029f6955bff20079468448) was detected as malicious by just 14 of 69 anti-malware engines.
FireEye’s analysis also found that the backdoor uses blocklists to detect forensic and anti-virus tools via processes, services, and drivers.
Microsoft has also been tracking these attacks, and has released Windows Defender updates to protect customers from the threat, which it has dubbed Solorigate.
In a security advisory, SolarWinds said versions 2019.4 HF 5 through 2020.2.1 of its Orion software are impacted, and it has advised customers to update to version 2020.2.1 HF 1 as soon as possible.
The company said annother update (version 2020.2.1 HF 2) is expected to be published on Tuesday, December 15, 2020, which will replace the compromised component and provide additional security enhancements.
U.S. government response to attacks
The Cybersecurity and Infrastructure Security Agency (CISA) has launched an investigation in cooperation with agency partners, and the Department of Homeland Security (DHS) issued Emergency Directive 21-01 on Sunday, instructing federal agencies to immediately investigate potential breaches involving their SolarWinds Orion installations and take steps to neutralize the threat.
Government organizations have been instructed to create forensic images of system memory and operating systems hosting Orion, analyze network traffic for IoCs, disconnect or shut down Orion systems, and identify and remove accounts and persistence mechanisms that may have been set up by the attackers.
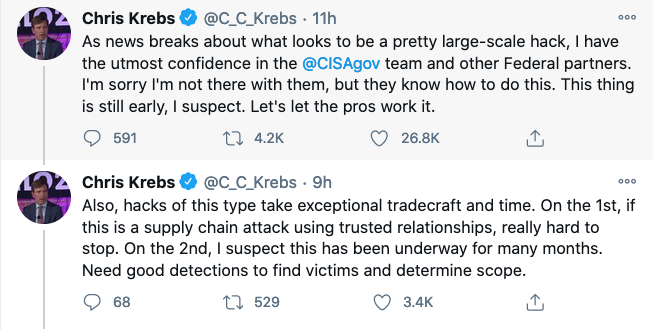
Christopher Krebs, former director of CISA, who was fired last month by U.S. President Donald Trump, took to Twitter to post several comments about the incident.
“If you’re a SolarWinds customer & use the below product, assume compromise and immediately activate your incident response team,” Krebs wrote.
Response from Russia
According to some reports, Russian state-sponsored threat actors are believed to be behind the SolarWinds attacks. In response to those reports, Russia’s embassy in the United States issued a statement on Sunday denying the allegations.
“We declare responsibly: malicious activities in the information space contradicts the principles of the Russian foreign policy, national interests and our understanding of interstate relations. Russia does not conduct offensive operations in the cyber domain,” the embassy said in its statement.
Much more fallout expected
While the initial focus of the campaign was on U.S. government agencies, several more victim organizations are likely to follow as security teams conduct invesgitations and companies prepare breach disclosures.
SecurityWeek will provide ongoing coverage of this threat, including additional resources for incident response teams.
Shares of publicly traded SolarWinds (NYSE: SWI) were trading down nearly 20% in pre-market trading on Monday.













