I am a millionaire. Actually, I’m a multi-millionaire. Or rather I could be if I helped the honorable Mr. Nagumba get his money out of Nigeria, or helped Barbara get her money out of Brazil, or picked up my unclaimed lottery winnings, or helped another half dozen people in the last month.
I have won $1500 several times a day for the last few months. I have won a new car. I have important packages waiting to pick up from FedEx and UPS. I am being audited by the IRS and they sent me an attachment that included an executable notice with instructions. I won a 15 day cruise if I qualified – they only needed a credit card number to confirm my identity and that I am over 18. I can get my teeth whitened or Lasik eye surgery for 80% off. I have qualified for a special deal on a new BMW 335 with experimental pricing, and can get in a brand new one for under $15,000. Two of my credit cards have been compromised so I needed to log onto the included website to verify and change my account information. As a matter of fact, another credit card that I don’t even have was also compromised, and I needed to log on there too. One of my bank accounts appears to have some out-of-date information associated with it. I can get really cheap Viagra (sic) cheap online, Heather thinks I’m hot, and there seems to be way too many people interested in my manhood.
My personal spam folder is pretty thin. I try to trim spam aggressively. Just in the last 24 hours I have received 42 emails. Three from family, 21 advertisements from retailers (it’s beyond me why I need a daily reminder from a retailer telling me that they are still open and selling the same stuff they’ve been selling for the last five years), and 18 spam. Now, I have no idea how much spam my ISP trims before it even gets to me, but I assume it is a lot. A quick search shows unofficial estimates that spam is somewhere between 60 and 97% of all email sent. By the best accounts I can find, that means around 40 billion spam emails every day (give or take a few billion). The numbers are down slightly from 2010 partially because three botnets (Rustock, Lethic, and Xarvester) have been somewhat throttled. The closure of spam specialist Spamit helped as well. But, as we all know, spam has not gone away.
Unfortunately, spam means money. Spam brings with it a variety of issues, but it also delivers chunks of money and other opportunities to those who generate it. Pay-per-click sites still exist, and if you send 100 million spam messages and get 1% of recipients to click through – ka-ching! Say you send 50 million spam messages that contain a link for a free virus scan, and you can get .5% of those recipients to follow through with a fake purchase for ONLY $29.99 – that’s $7.5million – ka-ching! Credit card information is not worth what it used to be, but if you can send 100 million fake “change your password” notices to BigBlueBank customers, and 1% of them go through your fake link and update their password – ka-ching! And even if they can’t get something from you, maybe they can compromise some low percentage of recipients with a Trojan or sniffer. The numbers add up quickly because of volume.
But spam and phishing emails are not always obvious, are they? Well, some of them are. If the email subject line includes things like “Cialis” or “Replica Handbags” I think the chances it is spam is probably something around 100%. But do we always know? I included an example of a recent phishing email I received (names have been changed). It looks pretty good at a glance, but there is a lot wrong with it if you pay attention.
Let’s look through it in detail.
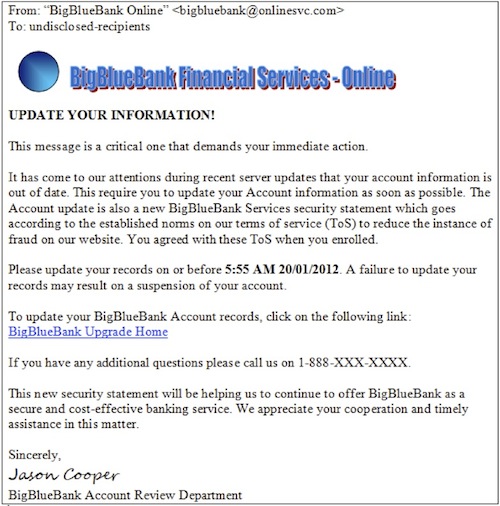
Let’s work on the premise that the logo and all the colors are correct, and that at a glance, this looks authentic – it appears to be an email from BigBlueBank, where you have an account registered with online access. What is wrong with the email?
1. BigBlueBank Online may be the correct name, but the chances that return email address is correct is low (read “low”, think “nonexistent”). Notice that it is @onlinesvc.com. If this was really from BigBlueBank chances are pretty good that it would be @BigBlueBank.com. If the return address just shows as BigBlueBank Online, hold your cursor over the name. The actual associated email address should show in a mouse-over or in the lower left corner of your browser.
2. “To: undisclosed-recipients” – If this was genuine, it would actually be to your specific email address, and NOT show as a bulk email with hidden addressees. Check what you bank emails you now – they are all to your real email address.
3. “UPDATE YOUR INFORMATION!” – This pushes an immediate sense of urgency. Not necessarily a blazing orange flag, but it should raise your skepticism when you get an email so obviously trying to raise your personal sense of alarm.
4. “This message is a critical one…” This is obviously a person to whom English is not their primary language. Normal English phrasing would be “This is a critical message…”. If BigBlueBank is based in South Carolina this should get your attention. If they are based in Germany, it probably still should, but not quite as much.
5. “It has come to our attentions,” “This require” – The extra “s” on attention and the missing “s” are perfect examples of disagreement in tense, and errors. These are strong indicators that the writer is not a natural English speaker, and that whoever sent the email did not spend enough time proof reading and editing the content. If BigBlueBank is a top 10 bank in the Americas, what are the chances that they would not have a proof reader check everything that went out (Hint: the answer is 0%).
6. “Your Account information” and “The Account update…” – What is with the random capitalization of “Account”? Errors like this should be blazing a hole in your brain by now.
7. “Is also a new BigBlueBank” – This is just an awkward sentence. Read the whole sentence from the email. Perhaps “the account update also includes” or something similar, but again, it is an error in grammatical construction that should tell you this is not a professional email.
8. “Services security statement…” – Again with the random capitalization of “Services”? Brain. Hole. Burning.
9. “Goes according” – Perhaps if it read “is in accordance” this would not raise alarms, but the misuse of the “ing” is a common error for a non-natural English speaker.
10. “On our terms of service” – “in” our terms of service would be appropriate for an English speaker, and even more appropriate in a professionally prepared communication.
11. 5:55 AM 20/01/2012 – This is actually the first thing I saw in the email that made me say “fake”. The date is shown as day/month/year, which is predominantly European or other international convention. Standard in the United States would be 01/20/2012. I know the other way sorts better, but it is aberrant construction in the U.S. If you are not from the U.S., this probably does not bother you as much as it did me.
12. “May result on a suspension of your account” – “on” is again wrong. A natural English speaker would say “in”. This also implies a threat designed to increase your sense of urgency and decrease your vigilance.
13. BigBlueBank Upgrade Home – Look at that. How convenient it was of them to include a link back to Bigbluebank for you. Just hold your mouse over the hyperlink (don’t bother; it won’t work on the example, since the hyperlink has been removed). By now you realize the chances that the link actually has anything to do with bigbluebank is exactly 0%. In the example of this email, it actually linked to something like the following – the fact that bigbluebank is not the domain should be an obvious clue: http//generalupdates.gh.ost.de/bigbluebank/account_update/index.php.
14. 1-888-XXX-XXXX – Very nice to have an included phone number. It really does help make the whole thing look better. Especially if you dial the number and someone in a call center answers it “Big Blue Bank – Customer Service, how can I help you?” First of all, check the provided number against the customer service number on your bank statements or against the number provided on Bigbluebank’s real website. It may be close but it will not match. Your second clue is that someone actually answered the phone and you did not have to go through a Voice Response system – when was the last time that happened?
15. “Will be helping” – there is that “ing” again. “This will help us” would not raise alarm, but the improper English should have your spinal column on fire by now. You should almost expect it say to “will to be helping us” like some alien speaking through an electronic translator.
If in doubt, bring up the genuine bigbluebank.com website by typing it into your browser yourself (completely ignoring their link, if you please), and check for information there. Locate their contact information to email, or call them to ask if they sent the information. Chances are that bigbluebank has its own security group that is interested in abuse and phishing emails. They may want you to forward a copy of the email to them for their own review if you feel like going that far.
Perhaps this was not the best example because this email was chock full o’ clues. But these are exactly the types of indicators you will see in many phishing emails. The fact that you even got this email should immediately raise your level of awareness, so everything else should follow.















