Encrypted email provider ProtonMail was hit by a significant distributed denial-of-service (DDoS) attack that appears to have been carried out by a group linked to Russia.
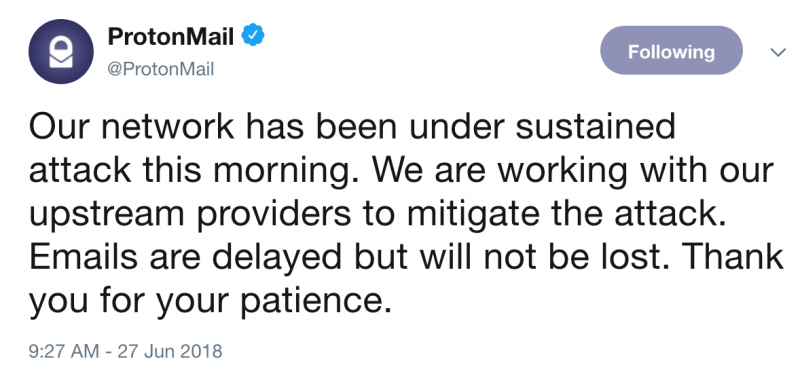
ProtonMail informed customers on Wednesday morning that its network was targeted in a sustained attack. The organization said that while emails would be delayed, they were not lost as a result of the incident. Some users reported that the attack impacted the ProtonVPN VPN service as well.
Services were restored roughly three hours after the initial announcement was made.
“The attacks went on for several hours, although the outages were far more brief, usually several minutes at a time with the longest outage on the order of 10 minutes,” ProtonMail stated.
The company says it deals with DDoS attacks on a daily basis, but this attack was more significant and its DDoS protection provider, Radware, needed more time than usual to prepare mitigations.
“While we don’t yet have our own measurement of the attack size, we have traced the attack back to a group that claims to have ties to Russia, and the attack is said to have been 500 Gbps, which would be among the largest DDoS’s on record,” ProtonMail said in a post on Reddit.
The DDoS attack on ProtonMail may have been significant, but it does not compare to a recent attack that hit an unnamed U.S.-based service provider, which peaked at 1.7 Tbps.
A few hours after ProtonMail announced the attack, Germany-based secure email service provider Tutanota also informed users that it had been experiencing a DDoS attack, but it’s unclear if the incidents are related. Tutanota told customers that services had been restored roughly one hour later.
UPDATE. Radware told SecurityWeek that it believes the attackers are actually based in the UK, not Russia.
“We can’t confirm attack size as it varied at different points in the attack. However we can confirm that the attack was high volumetric, multi-vector attack. It included several UDP refection attacks, multiple TCP bursts, and Syn floods,” Radware said.
Related: You Can DDoS an Organization for Just $10 per Hour














