After operating in stealth mode for roughly two years, Shape Security, a start-up founded by former Google, Department of Defense and defense contractor employees, has finally emerged from stealth mode and has launched its first product.
This week the company launched new class of security appliance designed to protect websites against cyber attacks stemming from malware and bots.
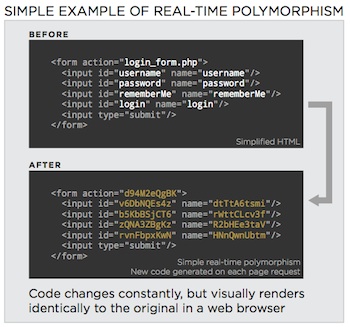
Dubbed the “ShapeShifter”, the solution is a 1U network security appliance that protects websites by leveraging real-time polymorphism—techniques that malware authors have used to evade anti-virus detection solutions.
![]() Shape says that it is taking the advantage away from attackers by implementing real-time polymorphism, or dynamically changing code, to remove the static elements that malware, bots and other automated attacks use to interact with web applications.
Shape says that it is taking the advantage away from attackers by implementing real-time polymorphism, or dynamically changing code, to remove the static elements that malware, bots and other automated attacks use to interact with web applications.
The appliance, what the company describes as a “botwall”, challenges attackers (or bots) by removing fixed web site elements to essentially transform web applications into moving targets transparently, while legitimate users see the original, unchanged user interface.
“We’re making it the attacker’s problem to figure out how to be able to create a scripted programmatic attack against an application which is constantly rewriting itself,” Shuman Ghosemajumder, Shape Security’s VP of Strategy, told SecurityWeek.
This approach allows enterprises to defend against multiple attack categories, such as account takeover, application DDoS, and Man-in-the-Browser attacks.
Automated attacks are nothing new, and security firms have been warning about them for years, though attackers are increasingly using automation in their ongoing attacks.
For example, in July 2013, Akamai Technologies warned in its State of the Internet Report that it was seeing a rise in account takeover attacks hitting e-commerce companies. In these attacks, automated attack tools and scripts known as “account checkers,” cybercriminals can easily determine valid user ID/password combinations across a large number of e-commerce sites. “Once an account is breached, attackers can collect a user’s personal data and credit card information to use for further fraud,” Akamai said at the time.
Shape’s Botwall also helps defend against some forms of automated business logic attacks—those that abuse the functionality of a program as opposed to an application vulnerability.
A 2012 study from Silver Tail Systems found that business logic attacks could often slip under the radar of development teams and cost enterprises time and money. According to the survey, 88 percent said business logic abuse is equally or more important than any other security issues facing their company at the time.
According to a July 2011 report from data security firm Imperva, web applications were probed or attacked about 27 times per hour or about once every two minutes.
“For years, attackers have used automated malware to conduct huge numbers of attacks on computer systems quickly and cheaply,” said Bob Blakley, director of security innovation at Citigroup.
“Modern cybercriminals employ sophisticated attacks that operate at large scale while easily evading detection by security defenses,” said Derek Smith, CEO of Shape Security. “The ShapeShifter focuses on deflection, not detection. Rather than guessing about traffic and trying to intercept specific attacks based on signatures or heuristics, we allow websites to simply disable the automation that makes these attacks possible.”
Currently with roughly sixty employees, the Mountain View, California-based company has raised $26 million in funding from high profile investors Kleiner Perkins Caufield & Byers, Venrock, Google Ventures, Wing Venture Partners, Allegis Capital and Eric Schmidt’s TomorrowVentures. Former Symantec CEO Enrique Salem has also put money into the company.

