Akamai Releases Q1 2013 ‘State of the Internet’ Report
Akamai Technologies has released its First Quarter, 2013 State of the Internet Report today, a report based on data gathered from its massive infrastructure and provides insights into global Internet statistics including network speeds, attack traffic, and threat analysis. The latest report has added new observations on “account checker attacks” that target e-commerce sites.
During the first quarter of 2013, Akamai said it spotted attempted account takeover behavior stemming from account checker attacks for numerous e-commerce organizations. These types of attacks have been increasingly popular, and happen when usernames and passwords stolen from websites are used to sign into other sites or services.
Using automated attack tools and scripts known as “account checkers,” cybercriminals can easily determine valid user ID/password combinations across a large number of e-commerce sites. “Once an account is breached, attackers can collect a user’s personal data and credit card information to use for further fraud,” Akamai said.
Akamai discovered that some attackers are using cloud and virtual private server providers to host their attack tools. Additionally, many of the account checkers scripts make use of open proxies for the actual attack, the report said, making it essentially useless to block the compromised systems.
“The tools Akamai has observed allow the attackers to use a list of open proxies and cycle through them after a fixed number of attempts,” the report noted. “The attackers need to ensure their list of proxies is both of sufficient size to disguise the attack and that it contains valid proxies, or they risk exposing their attack.”
There are a number of defenses that can be used by site operators to identify and stop these attacks, Akamai said, including CAPTCHA’s or other validation requiring user intervention, as most tools used in these types of attacks are not currently capable of bypassing these rather simple defenses.
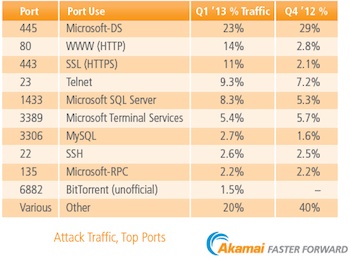 Attack Traffic and Top Ports Attacked
Attack Traffic and Top Ports Attacked
Akamai maintains a distributed set of unadvertised agents deployed across the Internet that log connection attempts, which are classified as attack traffic. Based on the data collected by these agents, Akamai is able to identify the top countries from which attack traffic originates, as well as the top ports targeted by these attacks. It is important to note that Akamai captures the source IP address of an attack, which does not positively determine the true location of an attacker.
Akamai said attack traffic was seen originating from 177 unique countries/regions during the first quarter of 2013. China maintained the number one spot as the largest volume source of observed attack traffic with 34 percent of the total (down from 41 percent in the previous quarter), Indonesia took over second place with 21 percent of observed traffic (up from 0.7 percent in the previous quarter).
Combined, more than half of the total observed attack traffic originated from China and Indonesia, while the top 10 countries/regions generated more than 80 percent of the observed attack traffic during the quarter.
The United States dropped from second to third with 8.3 percent of observed traffic, down from 10 percent in the previous quarter.
Port 445 (Microsoft-DS) continued to be the most targeted port in the first quarter, receiving 23 percent of observed attack traffic, Akamai said, while Port 80 (WWW HTTP) was second at 14 percent, a majority of which appeared to be originating in Indonesia.
DDoS Attacks
During the quarter, 154 different Akamai customers reported a total of 208 DDoS attacks, up slightly from the 200 reported in the previous quarter. Breaking down the attacks, 35 percent targeted Enterprise customers; 32 percent were focused on Commerce customers; 22 percent on Media customers; 7 percent on High Tech customers; and 4 percent targeted Public Sector customers.
Other interesting state provided in the report include:
• Global average connection speed rose 4 percent to 3.1 Mbps (up from 2.9 Mbps).
• Global average peak connection speeds increased 9.2 percent to 18.4 Mbps during the first quarter of 2013.
• Hong Kong was again number one at 63.6 Mbps, an increase of 9 percent over the previous quarter.
• Global broadband (>4 Mbps) adoption increased 5.8 percent during the quarter to reach 46 percent. Global high broadband (>10 Mbps) reached 13 percent on a 10 percent increase over last quarter.
• In Q1 2013, average connection speeds on surveyed mobile network operators ranged from a high of 8.6 Mbps to a low of 0.4 Mbps. Nine operators demonstrated average connection speeds in the broadband (>4 Mbps) range while 64 more operators showed average connection speeds above 1 Mbps.
“This quarter’s State of the Internet Report shows continued positive growth in terms of Internet and broadband adoption worldwide. We have seen overall increases in average and peak connection speeds along with greater broadband penetration on both a quarterly and annual basis,” said David Belson, the report’s editor. “However, the levels of malicious activity we’ve observed show no signs of abating, as evidenced by the ongoing rise in DDoS attacks. This reinforces the continued need for vigilance by organizations that are conducting business and maintaining a presence on the Internet.”
More than 733 million unique IPv4 addresses from 243 countries/regions connected to the Akamai Intelligent Platform, an increase of 3.1 percent over the previous quarter and 10 percent year over year, Akamai said. However, because a single IP address can represent multiple individuals or devices, Akamai estimates the total number of unique Web users connecting to its platform during the quarter to be well over one billion.
More on Akamai’s State of the Internet Reports can be found here.

