A new survey into cloud concerns undertaken by database security firm HexaTier provides no surprises: security risks (44%) followed by compliance and regulation (29%) are the two biggest factors preventing greater cloud adoption (although we are specifically talking about database as a service rather than cloud in general).

Tel Aviv, Israel-based HexaTier is a bit like a focused Cloud Access Security Broker (CASB). Rather than provide an overall security approach to the cloud in general, it focuses on protecting the three primary cloud database services: AWS, Azure and Google. It does this by using reverse proxy to examine everything that goes into the databases or comes out from them. This, like CASB in general, provides visibility and control into an otherwise obscured cloud environment.
What is surprising, however, is the rather common mistake of confusing security and compliance. The report suggests that the cloud can be more secure than on-premise security. “After all,” it notes, “can a typical organization compete with the overall security that giants like Amazon, Microsoft and Google are capable of implementing?” This is an argument that for many leading businesses has already been won.
The issue today is less about security and more about compliance. Compliance requires that you achieve security by being able to demonstrate what you do to ensure security. You cannot guarantee security against breaches; but if you can show that you have taken all reasonable steps to protect your data, you are less likely to be held culpable by the regulators when the unthinkable happens.
This, visibility into the cloud to see and control what is happening, is the big problem with cloud. This is what Hexatier’s technology seeks to provide – but again it is for the big database providers rather than the cloud in general. Companies will still need mainstream on-premise security to prevent legitimate downloads subsequently leaking out into the unprotected cloud via its own users’ Shadow IT.
“Regulatory compliance in the DBaaS environment is more complex than in traditional, on-premises databases, and currently available solutions are less mature,” notes the report.
Nevertheless, it remains hopeful. “It is very likely that, in the future, regulatory compliance of DBaaS will be as easy – or even easier – than for on-premises databases, because the tools and techniques for cloud-based compliance are continuously developing and improving.”
This is quite likely true – but unfortunately compliance requirements are growing and evolving just as fast. The big one on the horizon right now is what effect will Europe’s new General Data Protection Regulation have on worldwide cloud adoption and use? That simply remains to be seen.
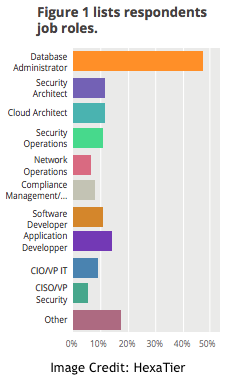
HexaTier’s report was compiled based on data from 574 respondents.












