New Browser Side-Channel Attack Doesn’t Require JavaScript
A team of researchers from universities in the United States, Australia and Israel has demonstrated that attackers could launch browser-based side-channel attacks that do not require JavaScript, and they’ve tested the method on a wide range of platforms, including devices that use Apple’s recently introduced M1 chip.
The researchers — representing the Ben-Gurion University of the Negev, the University of Michigan and the University of Adelaide — have published a paper on what they have described as the first browser side-channel attack that uses only CSS and HTML, and works even if JavaScript is completely disabled.
The analysis focused on Prime+Probe, a cache side-channel attack method that can detect which cache sets are accessed by the target and uses that to infer potentially valuable information.
Conducting these types of attacks in the browser typically involves the execution of JavaScript code and timing measurements. Web browsers vendors and third parties have been working on developing protections against such attacks, including by limiting or completely preventing JavaScript execution and by trying to prevent attackers from precisely measuring time.
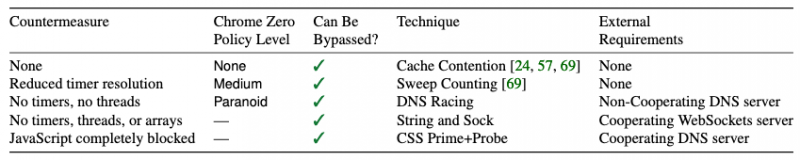
The researchers have developed a sequence of attacks where they have progressively decreased dependency on JavaScript features, which resulted in a method that relies entirely on HTML and CSS. They claim to have shown that all existing countermeasures can be bypassed.
The attack method has been successfully tested — with various levels of success depending on the targeted architecture and existing mitigations — against hardened browser environments (e.g. Tor, Chrome Zero, DeterFox) on devices with Intel, AMD, Samsung and Apple chips.
Impacted vendors have been notified. Apple told the researchers that the public disclosure of their findings does not raise any concerns.
“We show that advanced variants of the cache contention attack allow Prime+Probe attacks to be mounted through the browser in extremely constrained situations,” the researchers said in their paper. “Cache attacks cannot be prevented by reduced timer resolution, by the abolition of timers, threads, or arrays, or even by completely disabling scripting support. This implies that any secret-bearing process which shares cache resources with a browser connecting to untrusted websites is potentially at risk of exposure.”
Related: New Technique Improves Effectiveness of Timing Channel Attacks
Related: New Side-Channel Attack Targets Intel CPU Ring Interconnect














