There was a significant increase in ransomware-related data leaks and interactive intrusions in 2021, according to the 2022 Global Threat Report released on Tuesday by endpoint security firm CrowdStrike.
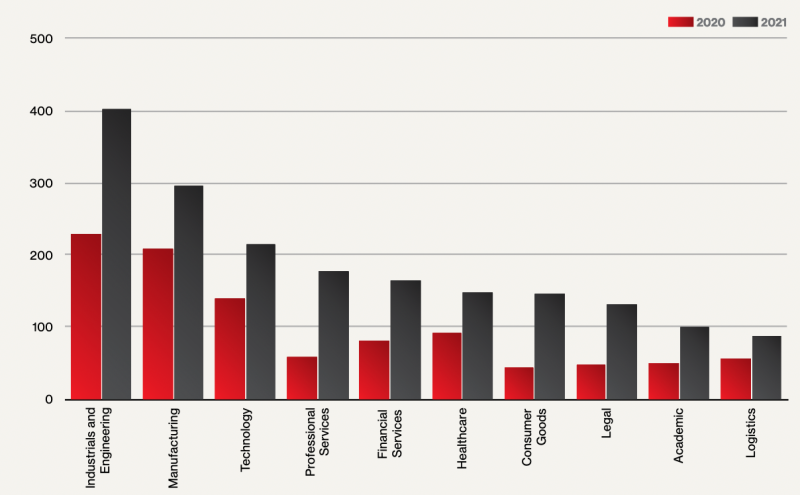
The number of ransomware attacks that led to data leaks increased from 1,474 in 2020 to 2,686 in 2021, which represents an 82% increase. The sectors most impacted by data leaks in 2021 were industrial and engineering, manufacturing, and technology.
“The growth and impact of [big game hunting] in 2021 was a palpable force felt across all sectors and in nearly every region of the world. Although some adversaries and ransomware ceased operations in 2021, the overall number of operating ransomware families increased,” CrowdStrike said in its report.
[ READ: Swissport Investigating Ransomware Group’s Data Leak Claims ]
As for interactive intrusions, which involve hands-on-keyboard activity, CrowdStrike saw a 45% increase in 2021, with 62% of attacks involving no malware, only hands-on activity. Nearly half of interactive intrusions were conducted by profit-driven cybercriminals — the cybersecurity firm calls it eCrime activity.
In these eCrime attacks, the average breakout time — the time it took the attacker to move laterally from the initially compromised system to another host within the victim’s network — was 1 hour and 38 minutes.
CrowdStrike added 21 new named adversaries to its database last year and the company now tracks a total of more than 170 threat groups.
The company’s report highlights disruptive operations linked to Iran, with threat actors and activity clusters using “lock-and-leak” tactics to target organizations in the United States, Israel and the MENA region.
“Lock-and-leak operations are characterized by criminal or hacktivist fronts using ransomware to encrypt target networks and subsequently leak victim information via actor-controlled personas or entities,” CrowdStrike explained. “Since they inauthentically operate as a criminal or hacktivist entity, these types of operations conduct activity beneath a veneer of deniability. Through the use of dedicated leak sites, social media and chat platforms, these actors are able to amplify data leaks and conduct [information operations] against target countries.”
The report also highlights China-linked activity, with China being named the “leader in vulnerability exploitation.” The number of new security flaws exploited by Chinese threat actors in 2021 was 12, six times higher than in 2020.
While it’s not uncommon for Chinese threat actors to develop exploits for their targeted intrusions, they have typically leveraged exploits requiring user interaction, such as opening malicious documents or accessing websites hosting malicious code. However, in 2021, they appeared to shift focus to security holes affecting internet-facing devices or services.
The complete 2022 Global Threat Report (PDF) is available on CrowdStrike’s website.
Related: Russian State-Sponsored Hackers Are Fastest: CrowdStrike
Related: Telecom Sector Increasingly Targeted by Chinese Hackers: CrowdStrike













