Foxsemicon Integrated Technology, a subsidiary of Taiwanese electronics giant Foxconn, appears to have been targeted by the notorious LockBit ransomware group.
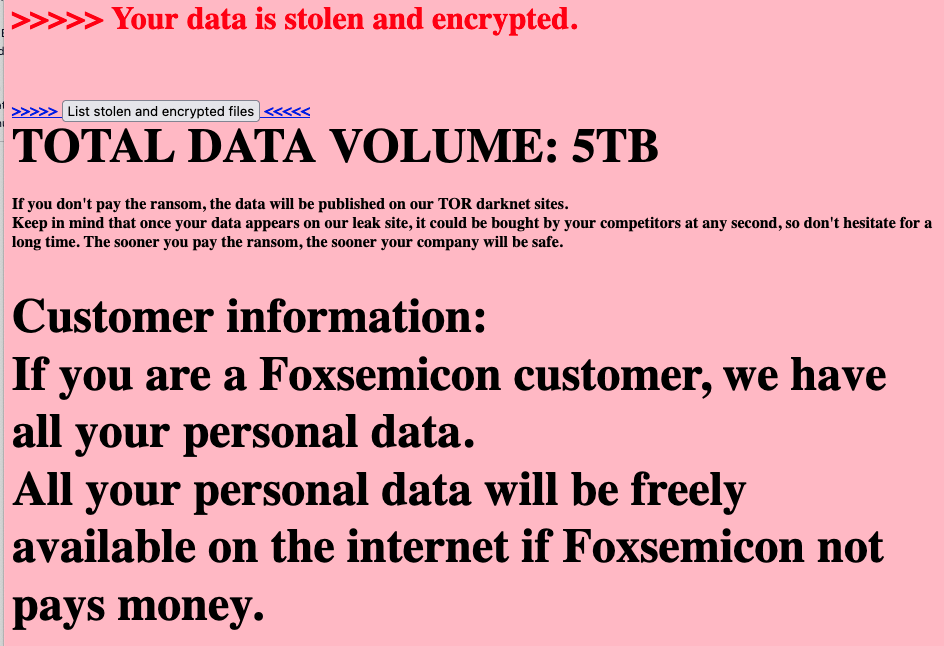
Foxsemicon specializes in semiconductor equipment manufacturing. The company’s website was defaced this week with a message claiming that data has been stolen and encrypted. The message said 5 Tb of data has been taken from the company’s systems.
The cybercriminals claimed to have obtained personal data belonging to customers and employees, and threatened to make it public on their leak website unless a ransom is paid.
The hackers’ message told employees that they will lose their job as they are allegedly “able to completely destroy Foxsemicon with no possibility of recovery”. It’s not uncommon for ransomware gangs to exaggerate their claims in an effort to put more pressure on the victim.
The message posted on the defaced website also advised the company not to contact any ransomware recovery services or insurance firms. The exact ransom amount is unclear, but this part of the message does mention a $1 million ransom as an example.
While the incident may turn out to have a big impact, Foxsemicon told the Taiwan Stock Exchange that its initial assessment indicates the incident should not have a significant impact on its operations.
The Foxsemicon website has been restored at the time of writing.
The ransomware group did not name itself on the defaced Foxsemicon website, but the links provided to the company point to the LockBit Tor-based leak website.
LockBit does not typically deface victims’ websites, but major ransomware groups have been known to experiment with various tactics to increase their chances of getting paid.
Foxsemicon has yet to be listed on LockBit’s site. The cybercrime gang, which has been running the world’s largest and most active ransomware operation, has targeted several other semiconductor companies in the past year, including Taiwan Semiconductor Manufacturing Company (TSMC), from which it initially demanded a $70 million ransom.
Related: Russian National Arrested, Charged in US Over Role in LockBit Ransomware Attacks
Related: US Organizations Paid $91 Million to LockBit Ransomware Gang
Related: LoanDepot Takes Systems Offline Following Ransomware Attack

















