It is no secret malware kits have been the source of many of the infections plaguing users in recent years. This trend is epitomized by Poison Ivy, a remote administration tool (RAT) at the heart of the Nitro attacks targeting the chemical and defense industries.
In a new research paper, Microsoft chronicled how Poison Ivy works and why it continues to be utilized by attackers. For one thing, the tool is available for free.
“Poison Ivy has an official website from which the kit is distributed. It is also available on a variety of underground websites and forums,” according to the Microsoft report. “This free and open distribution is growing increasingly uncommon as the malware authors of today tend to operate exclusively within their trusted circles and sell their creations to the highest bidders.”
According to Microsoft, Poison Ivy uses a client/server architecture to essentially turn victim machines into “servers” that operators can then connect to and remotely control.
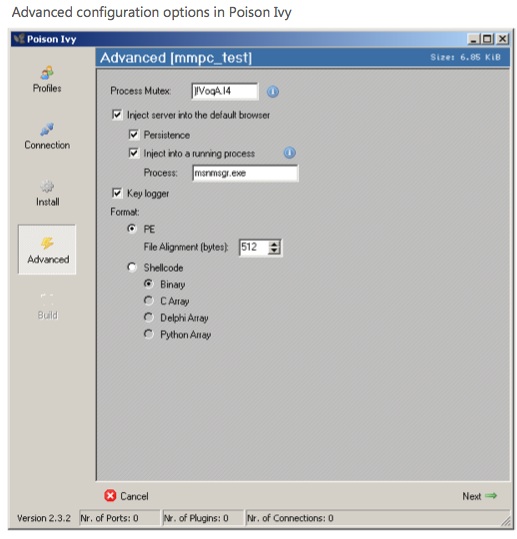
“The malware is considered a kit because operators can configure the server application to their liking before generating a server assembly that is then distributed and covertly installed on victim systems,” the Microsoft researchers wrote in the paper. “These server assemblies are very small (generally between 7 KB and 10 KB). The kit also contains a “client” component that a controller can use to remotely access and control compromised systems.”
Once on an infected system, the malware enables an attacker to download and upload files remotely, log keystrokes, inject malicious code and perform other malicious activities. The malware is distributed in a variety of ways, from software vulnerabilities to phishing e-mails, with the latter being how Poison Ivy infiltrated RSA earlier this year. Poison Ivy was also linked to the GhostNet spy operation uncovered in 2009, as well as the Nitro attacks recently publicized by Symantec.
“With Poison Ivy there’s the option to pay the author for customized versions,” Roel Schouwenberg, senior researcher at Kaspersky Lab, told SecurityWeek. “However, we believe that in these APT-style attacks the attackers customize Poison Ivy themselves.”
Officials at Microsoft said the company has removed Poison Ivy from some 16,000 infected machines as of last month. In the report, researchers note the United States has been the hardest hit in 2011, accounting for 12 percent of infections. Second and third on the list are Korea and Spain, which registered nine and seven percent, respectively.
The Microsoft paper can be downloaded here.
















