A researcher has released a proof-of-concept (PoC) exploit for a recently patched Windows vulnerability that could allow remote code execution and which has been described by Microsoft as wormable.
The flaw, tracked as CVE-2021-31166 and rated critical severity, was discovered internally by Microsoft and it was patched by the tech giant with its May 2021 Patch Tuesday updates.
The vulnerability affects the HTTP Protocol Stack (http.sys) and exploitation does not require authentication or user interaction.
“In most situations, an unauthenticated attacker could send a specially crafted packet to a targeted server utilizing the HTTP Protocol Stack (http.sys) to process packets,” Microsoft explained in its advisory.
The vulnerability only impacts recent versions of Windows 10 and Windows Server, which means it can only be used against certain systems. However, in its advisory, Microsoft assigned it an “exploitation more likely” rating.
“[http.sys] is a Windows-only HTTP server which can be run standalone or in conjunction with IIS (Internet Information Services) and is used to broker internet traffic via HTTP network requests,” McAfee’s Steve Povolny explained in a blog post describing the flaw.
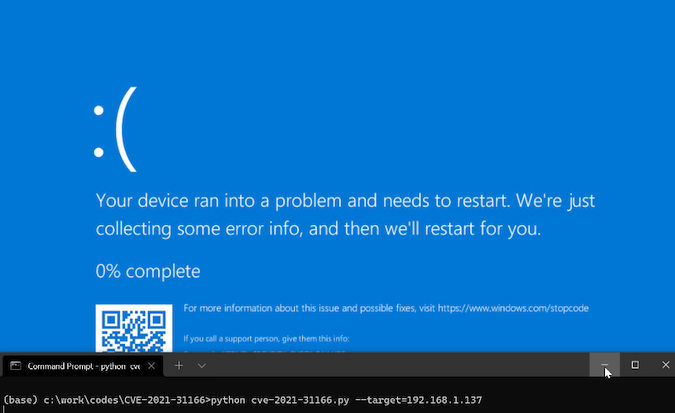
“The issue is due to Windows improperly tracking pointers while processing objects in network packets containing HTTP requests. As HTTP.SYS is implemented as a kernel driver, exploitation of this bug will result in at least a Blue Screen of Death (BSoD), and in the worst-case scenario, remote code execution, which could be wormable,” Povolny said.
“While this vulnerability is exceptional in terms of potential impact and ease of exploitation, it remains to be seen whether effective code execution will be achieved. Furthermore, this vulnerability only affects the latest versions of Windows 10 and Windows Server (2004 and 20H2), meaning that the exposure for internet-facing enterprise servers is fairly limited, as many of these systems run Long Term Servicing Channel (LTSC) versions, such as Windows Server 2016 and 2019, which are not susceptible to this flaw,” he added.
Researcher Axel Souchet over the weekend announced the release of a PoC exploit for CVE-2021-31166. However, his PoC does not achieve remote code execution — it shows how an attacker can leverage the flaw to cause a DoS condition on the targeted system by sending it specially crafted packets.
Related: PoC Released for Unpatched Windows Vulnerability Present Since 2006
Related: Microsoft Probing Possible PoC Exploit Code Leak
Related: PoC Exploit Released for Unpatched Flaw Affecting Chromium-Based Browsers
Related: Cybersecurity Community Unhappy With GitHub’s Proposed Policy Updates














