LONDON – BLACK HAT EUROPE – Researchers have discovered a new attack method that could allow malicious actors to disrupt and manipulate the physical processes managed by programmable logic controllers (PLCs) without being detected.
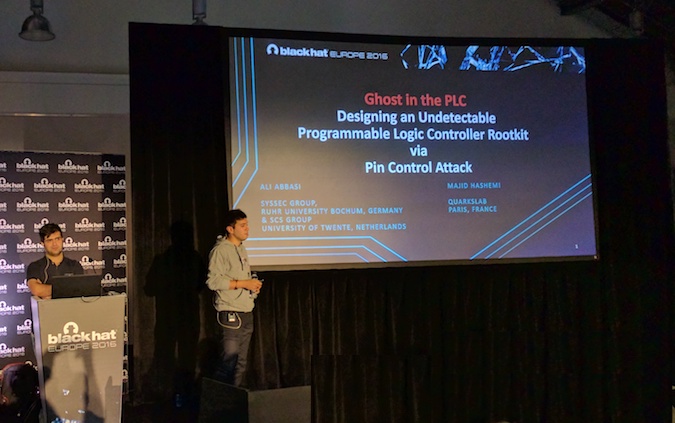
The attack method was detailed on Thursday at the Black Hat Europe 2016 security conference by Ali Abbasi, a Ph.D. candidate in the distributed and embedded system security group at the University of Twente in the Netherlands, and Majid Hashemi, a research and development engineer at Quarkslab in France.
PLCs are devices used to control and monitor physical processes in industrial environments. In the past years, security experts demonstrated on several occasions the risks posed by vulnerabilities in PLC software and firmware, and they even showed how attackers could develop a worm that spreads from one PLC to another.
However, Abbasi and Hashemi have come up with a new post-exploitation attack method that does not involve any modifications to the PLC firmware or logic. Instead, it involves manipulating the device’s input and output (I/O) at a low level, which allows the attacker to control the PLC without triggering any alarms.
A PLC can receive and transmit various types of electrical and electronic signals. The input, which typically comes from sensors, and the output, which can be used to control motors, valves or relays, are linked to input and output pins on an integrated circuit known as a system on chip (SoC). The SoC’s pin controller can configure the modes of a pin (i.e. they are set to serve as input or output) and configure pin multiplexing, which allows the use of a pin for different purposes via a switch.
The experts discovered that an attacker who has compromised the PLC can tamper with the input and output without being detected and without alerting the operators monitoring the process through a human-machine interface (HMI).
Abbasi and Hashemi have identified two pin control attack methods. One of them, which involves changing the pin’s configuration, allows a piece of malware that is present on the PLC to switch a pin from input to output and vice-versa. The second attack type, which involves multiplexing, is similar, but it involves changing the functionality of the same pin.
This can cause the system controlled by the PLC not to perform its intended function (e.g. not opening a valve to adjust pressure). The attacker can also take control of the system (e.g. arbitrarily close or open the valve).
However, the PLC’s operating system and the user are not alerted as the I/O pin values are normal in the virtual I/O registers. Another advantage of this attack is that it can bypass host-based intrusion detection systems such as Autoscopy Jr. and Doppelganger.
The attack can be implemented through a rootkit, which requires root access to the targeted system, but it can also be carried out without root access. In the second scenario, in which the attacker has the same privileges as the PLC runtime, the attack can be conducted via a remote code execution vulnerability.
Both attacks can be used to cause a denial-of-service (DoS) condition and to control the physical process connected to the PLC. However, the experts pointed out that the non-root variant is more efficient, especially from a performance standpoint, but it’s less precise.
“The novelty of our attack lies in the fact that to manipulate the physical process we do not modify the PLC logic instructions or firmware,” the researchers said in their paper. “Instead, we target the interaction between the firmware and the PLC I/O. This can be achieved without leveraging traditional function hooking techniques and by placing the entire malicious code in dynamic memory (in rootkit version of the attack), thus circumventing detection mechanisms such as Autoscopy Jr. and Doppelganger. Additionally, the attack causes the PLC firmware to assume that it is interacting effectively with the I/O while, in reality, the connection between the I/O and the PLC process is being manipulated.”
The researchers have not disclosed the names of any vendors, but based on the analysis of several CPU architectures commonly used in PLCs, they believe a majority of them are affected. Vendors have been made aware of the attack method, but it’s unclear if they plan on addressing these issues in the near future, the researchers told SecurityWeek in an interview.
Abbasi and Hashemi pointed out that PLCs have many vulnerabilities that are more easy to exploit compared to the weaknesses they disclosed, especially when an attacker has root access to a device. However, the easy-to-exploit flaws are also easier to address, which could lead to malicious actors turning to less obvious security holes in the future, such as the one found by Abbasi and Hashemi.
The experts said their goal is to raise awareness and convince vendors to design products that are even more secure. Their paper also includes a series of recommendations on how these types of attacks can be detected.
















