The Control System Cyber Security Association International (CS)2AI and KPMG on Monday announced their first annual cybersecurity report focusing on industrial control systems (ICS) and operational technology (OT).
(CS)2AI, a non-profit organization, has more than 16,000 members worldwide and the report is based on information provided by 600 of them. Respondents represent all continents — although nearly half of them are from North America — and a wide range of industries and organization sizes. More than 80% of respondents are decision makers when it comes to OT security expenditure.
(CS)2AI released a preview of the report last year at SecurityWeek’s ICS Cyber Security Conference in Atlanta. The organization revealed at the time that some respondents claimed to have experienced ICS security incidents that resulted in injury and even loss of life.
The final version of the report covers a wide range of topics, including control system cybersecurity prioritization, budgets, staffing, awareness training, vulnerabilities, organizational plans, managed services, assessments, network monitoring, frameworks and technologies, and incidents.
Of the incidents observed by respondents in the year prior to taking part in the survey, a majority involved an email-based attack vector (32%) or an infected removable media drive (35%). Nearly 46% of attacks have been attributed to negligent insiders (i.e. individuals with trusted access who unwittingly facilitate or cause a breach), but some were also attributed to scammers (16%), cybercriminals (14%), nation-state actors (12%) and malicious insiders (11%).
Learn more at SecurityWeek’s 2020 ICS Cyber Security Conference and SecurityWeek’s Security Summits virtual event series
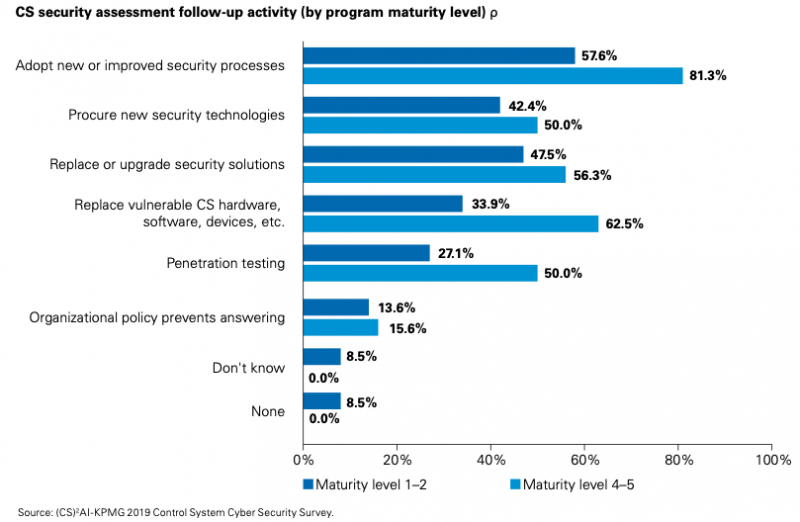
Much of the data in the report is presented separately for organizations with a more mature cybersecurity program and organizations with a less mature program.
(CS)2AI noted that organizations with a mature program are more likely to detect the involvement of social engineering in an attack (12% for those with a mature program vs 4% for less mature program), or nation-state actors (20% vs 13%).
(CS)2AI has highlighted some interesting differences between organizations with a mature cybersecurity program and ones with a less mature program.
For instance, 47% of organizations with a mature program use managed services for ICS cybersecurity, compared to only 5% of companies with a less mature program. Additionally, those with a mature program conduct end-to-end security assessments more frequently (53% vs 36%).
The report also shows that companies with a mature program are much more likely to replace vulnerable hardware or software after an assessment (63% for mature programs vs 34% for less mature programs).
Derek Harp, founder and chairman of (CS)2AI, told SecurityWeek that they will continue to collect data, which will enable the organization to regularly identify trends in this area.
Related: Over 70% of ICS Vulnerabilities Disclosed in First Half of 2020 Remotely Exploitable
Related: Over 400 ICS Vulnerabilities Disclosed in 2019: Report
Related: Honeywell Sees Rise in USB-Borne Malware That Can Cause Major ICS Disruption












