A newly identified NTLM (New Technology LAN Manager) relay attack abuses a remote procedure call (RPC) vulnerability to enable elevation of privilege, researchers from cybersecurity firm SentinelOne reveal.
The security hole, which apparently affects all versions of Windows, enables an attacker to escalate privileges from User to Domain Admin, all without requiring interaction from the user (NTLM relay attacks typically do require user intervention).
The researchers used a DCOM client that was instructed to connect to a RPC server, operation that involved two NTLM authentications, one without the “Sign flag” being set, and also leveraged the fact that the DCOM activation service can be abused to trigger RPC authentication.
The idea behind the attack, SentinelLabs explains, was that a shell in Session 0, even as a low privileged user, combined with triggering some CLSIDs, could allow the attacker to obtain “an NTLM authentication from the user who is interactively connected.”
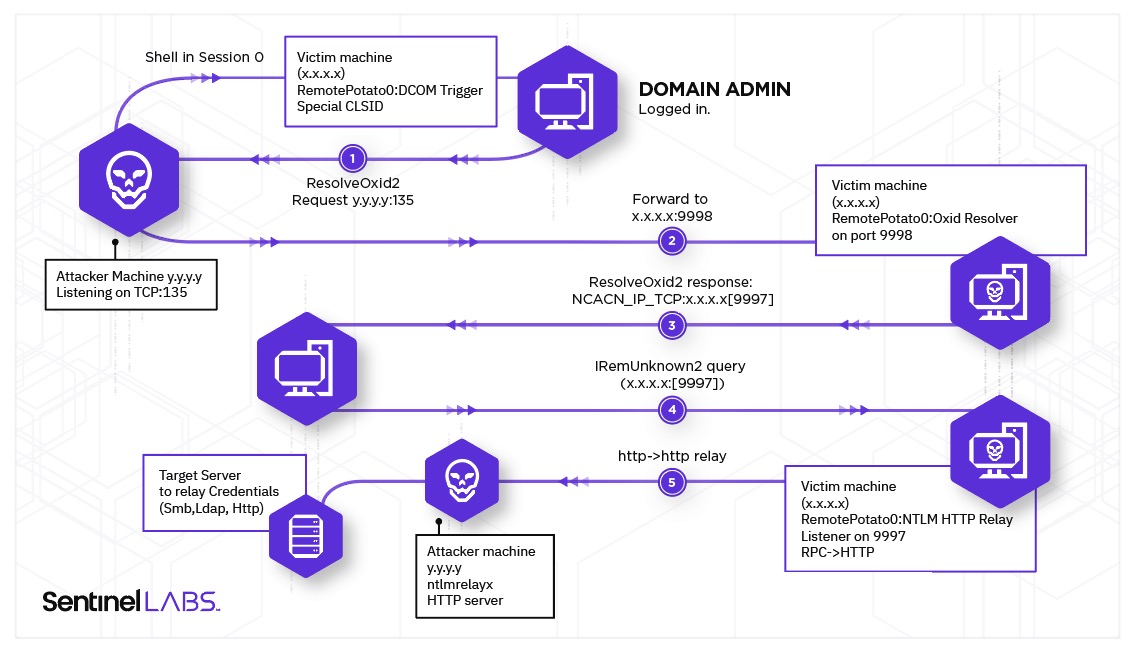
The attack works as follows: the attacker has a shell in Session 0 on the target machine, even with a low privileges account; a user with high privileges (such as Domain Admin) logs in interactively; the attacker triggers the DCOM activation service to impersonate the high-privileged user; the attacker implements a man-in-the-middle to receive an authenticated call; the binding of the RPC under the attacker’s control takes place; the victim machine makes an authenticated call; authentication is relayed to a privileged resource such as LDAP, SMB, HTTP or other; the authentication is forwarded for privilege escalation.
SentinelLabs also released proof-of-concept code to demonstrate how the exploit works, and reveals that, although Microsoft has acknowledged the vulnerability, a patch won’t be released.
The researchers, however, did publish a series of mitigations that should help prevent attacks that would trigger an authenticated RPC/DCOM call and then relay the NTLM authentication.
“This is different from other known techniques such as CVE-2020-1113 and CVE-2021-1678, where relaying happens between a generic ‘client’ protocol vs. an RPC server. In this case, we had an RPC client whose authentication was relayed to other ‘server’ protocols and without ‘victim’ interaction. Therefore, we hope that MS reconsider their decision not to fix this serious vulnerability,” SentinelLabs concludes.
Related: CrowdStrike Discloses Details of Recently Patched Windows NTLM Vulnerability