A brand new ransomware family currently being distributed through the Magnitude exploit kit appears to be targeting South Korean users exclusively, security researchers have discovered.
Dubbed Magniber, the threat checks the language of the compromised systems and only fully executes on machines featuring the locale identifier string 0x0412, which is the identifier for Korean, Trend Micro reports.
The new malware family was first observed this week, when Magnitude returned to activity after nearly a month of silence. The EK was usually distributing the Cerber ransomware, but it appears that its operators have moved to other payloads.
While most of the Magnitude attacks over the past two months and a half focused on Taiwan (81%), the security researchers noticed a shift toward South Korea on October 15. Magnitude campaigns use malvertising to infect users and deliver malicious payloads by exploiting the Internet Explorer vulnerability CVE-2016-0189, which Microsoft patched in May 2016.
Magnitude was the last exploit kit to have delivered Cerber, which appears to have disappeared from the threat landscape last month. Now, the toolkit is pushing a ransomware family that apparently uses the same payment system as Cerber.
This is why the security researchers who discovered the threat called it Magniber (Magnitude+Cerber), although there doesn’t seem to be code base resemblance between the two, Bleeping Computer’s Lawrence Abrams notes.
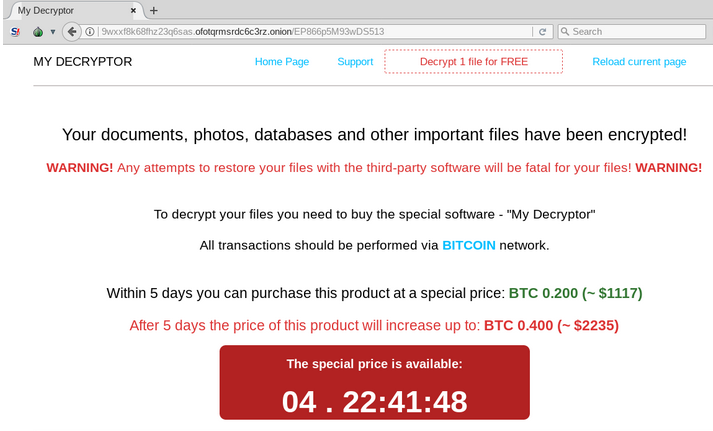
Specific to the new malware is the fact that it uses the victim’s unique ID as a subdomain to the payment portal on Tor. This subdomain is then displayed in the ransom note deployed on the infected system.
Once on the infected system, the malware starts searching for files to encrypt. At the moment, it is targeting over 700 file types, Malwarebytes says. The ransomware avoids encrypting files located in folders such as Windows, Program Files, Boot, Recycle Bin, Local Settings, and several Documents and Settings subfolders, among others.
According to Trend Micro, Magniber’s code shows that the ransomware might still be under development. According to them, the threat could be still in experimental stages, supposedly built by Magnitude’s developers.
“Indeed, we’re bound to see more developments in both Magnitude and Magniber as their capabilities and tactics are fine-tuned. While Magnitude’s distribution of Magniber is still relatively muted, their ability to exploit security gaps in the system and encrypt its files makes their combination a credible threat,” the security researchers note.
According to Abrams, files encrypted by Magniber can be decrypted for free, so victims should refrain from paying the ransom. All users, however, are advised to keep their applications and operating systems updated at all times, and to install and maintain an anti-virus solution to avoid being infected in the first place. Users should also back up their data at all times, for easy recovery in the event of an infection.
Related: Ransomware – Where It’s Been and Where It’s Going
Related: Exploit for Recently Patched Flash Flaw Added to Magnitude EK

