The existence of a previously unknown infection technique used by spyware firm NSO Group is suggested by a single line in a contract between NSO and the telecom regulator of Ghana.
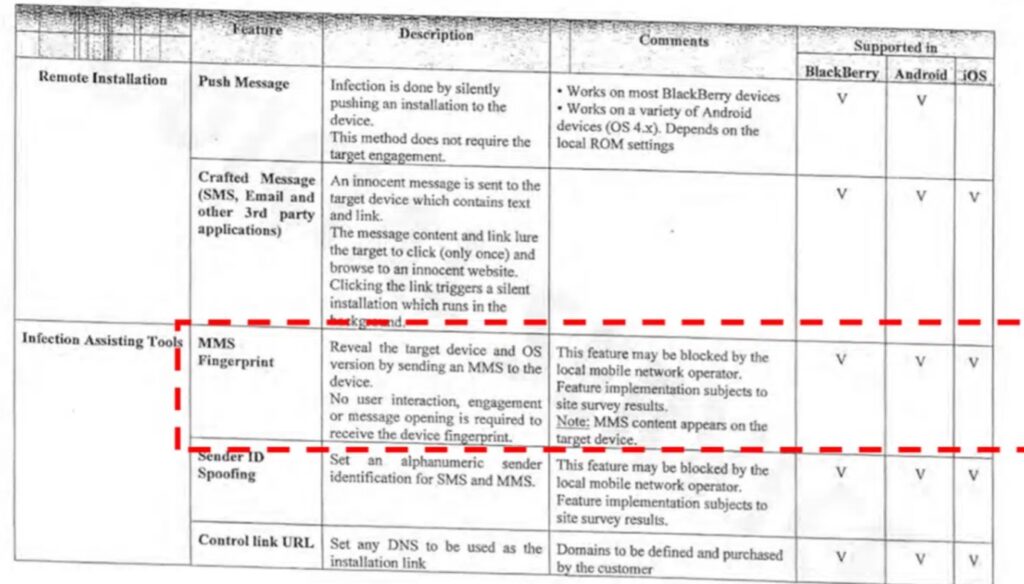
The contract is within the documentation of the ongoing court case between WhatsApp and NSO. Labeled under ‘Infection Assisting Tools’ is a single entry titled ‘MMS Fingerprint’. NSO claims it can reveal the target device and the OS of the target device, ‘without user interaction, engagement or message opening’, and can be used against Android, Blackberry, and iOS.
There is (or has been) no known MMS fingerprint infection route. Cathal McDaid, VP of technology at Swedish telecoms security firm Enea investigated to learn more.
Since multiple device manufactures can be targeted, McDaid decided to look at the MMS flow rather than the individual devices. The MMS flow, writes McDaid, is somewhat ‘messy’: “Confusingly, sometimes the MMS flow is not using MMS.”
MMS was introduced when not all phones were MMS compatible. So, the developers introduced a fall-back to a type of SMS known as a binary SMS (WSP Push), used to notify the recipient MMS device’s user agent that an MMS message is waiting for retrieval.
Similarly, retrieval of the message is also not specifically ‘MMS’ – it is an HTTP GET request to the URL address contained in the waiting message. “The interesting thing here,” writes McDaid, “is that within this HTTP GET, user device information is included. It was suspected that this may be the point that targeted device information could be leaked, and the MMS Fingerprint could be ‘lifted’.”
Enea tested this. Via MMS it was able to make the target device perform a GET to an URL on a server it controlled. This HTTP GET exposed the device’s UserAgent and x-wap-profile fields. The first identifies the OS and device. The second points to a UAProf (User Agent Profile) file that describes the capabilities of a mobile handset. Enea concealed the process by changing the binary SMS element to be a silent SMS through setting a TP-PID value of 0x40. The result was that no MMS content appears on the targeted device, and the targeted person sees nothing on their phone.
All of this describes a possible infection route (which is what the NSO contract claims) rather than a specific device exploitation. However, with the information obtained, further attacks are simplified. “Both of these can be very useful for malicious actors,” says McDaid. “Attackers could use this information to exploit specific vulnerabilities or tailor malicious payloads (such as the Pegasus exploit) to the recipient device type. Or it could be used to help craft phishing campaigns against the human using the device more effectively.”
To a degree, this is all theory – but Enea has demonstrated that it is a workable MMS fingerprinting method. The firm has found no indication of it being used in the wild, but notes that it doesn’t have visibility into every operator in the world. It can be blocked by the local mobile network, while subscribers could disable MMS auto-retrieval on their handset (as recommended to defend against other MMS exploits such as Stagefright.
There is no indication that this MMS fingerprinting is being used, and it can be blocked – but it exists and NSO has indicated its availability.
Related: NSO Group Used at Least 3 iOS Zero-Click Exploits in 2022: Citizen Lab
Related: El Salvador Journalists Sue NSO Group in US Over Alleged Pegasus Attacks
Related: Report: L3 Emerges as Suitor for Embattled NSO Group
Related: Spanish Judge to Seek Testimony From NSO on Pegasus Spyware


