A new report from Juniper Networks outlines the trends and the year-over-year growth of the mobile malware market, including the fact that criminals are making a tidy profit as a result of their efforts.
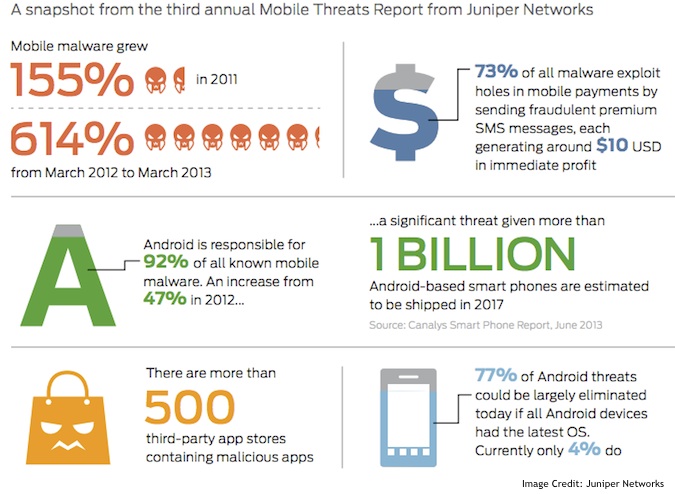
Monitoring from March 2012 until March 2013, Juniper charted the growth in the mobile malware market, and noticed a few patterns – most notably the fact that criminals have turned the process into a vast money making enterprise. The number of mobile threats grew rapidly during the monitoring period – spiking an astounding 614% to 276,259 malicious apps in all, which the company says proves that criminals are showing a major interest in mobile development.
Purely focusing on the stats, as seen in the graphic below, criminals are making $10 USD in profit per-install. A majority of those profits come from messages sent to premium SMS numbers. When it comes to making money, criminals are seeing close to a 92% ROI, by focusing on Android, thanks largely to the number of devices on the market with fragmented versions.
To compile its Mobile Threats Report report, Juniper analyzed more than 1.85 million mobile applications and vulnerabilities across major mobile operating system platforms.
Targeting outdated deployments means a wider surface to attack, but the process is cheaper – so criminals don’t have to spend all that much for new attacks. In fact, Juniper’s third annual Mobile Threats Report noted an increase in mobile malware development between October and January, which is the sale cycle for new devices.
So as consumers purchase the discounted models to save some money, the criminals are targeting them with rather known exploits. Google has a great track record for fixing these bugs, but the carriers don’t patch fast enough – if they patch at all – creating a type of open season for criminals.
At the same time, they also look to target the new devices with malware focused on information gathering and remote access – which was seen in the growth of the NotCompatible campaign.
As reported earlier this week by SecurityWeek, the NotCompatible malware was recently spotted circulating via compromised email accounts. Juniper noticed the same trend during their monitoring period as malicious Phishing messages started hammering enterprise networks.
“There’s no doubt mobility will continue to be a pervasive and disruptive force across every industry. We have found that it has created an easy business opportunity for malware developers who are becoming savvy in their approach to quickly turn profits in a rapidly growing market,” commented Troy Vennon, director of the Mobile Threat Center, Juniper Networks. With Juniper’s findings showing mobile is seeing a similar evolution to that of PC-based threats, its clear that mobile attacks will continue to increase and they’ll become more sophisticated in the coming years.
With that said, there’s no going back for enterprise operations, mobile is a way of life, and it’s quickly becoming an essential part of business. This is why BYOD is such a hot topic, because employees want to use their own devices for work and play, and more often than not – corporations are trapped in the middle.
The full report is available online.
“What enterprise is unable to do at this point is tell their users no, they cannot use their device in their environment. They’re not going to be able to get around it,” Vennon said.

