The US Cybersecurity and Infrastructure Security Agency (CISA) and the nonprofit organization MITRE have published the 2022 list of the 25 most dangerous vulnerabilities.
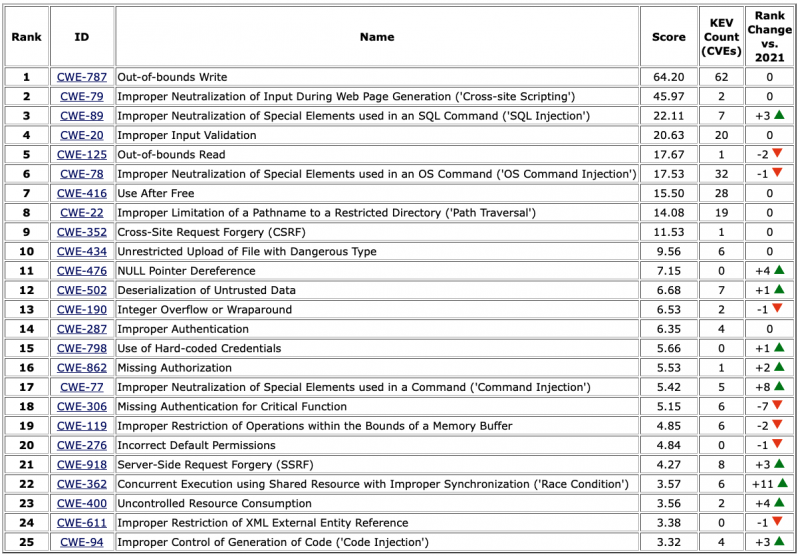
The 2022 CWE Top 25 Most Dangerous Software Weaknesses list contains the most common and impactful weaknesses, and is based on the analysis of nearly 38,000 CVE records from the previous two years.
Out-of-bounds write and cross-site scripting (XSS) remain the two most dangerous vulnerabilities.
Some of the most significant changes include race conditions moving from 33 to 22, code injection from 28 to 25, and uncontrolled resource consumption from 27 to 23 — these are also the new types of vulnerabilities that made the 2022 list. Command injection and NULL pointer dereference also moved up a few positions in the list.
Three types of vulnerabilities were removed compared to the 2021 list: exposure of sensitive information to an unauthorized actor (fell to 33), insufficiently protected credentials (fell to 38), and incorrect permission assignment for critical resources (fell to 30).
One significant change in the methodology used to build the 2022 CWE Top 25 is related to the use of data from CISA’s Known Exploited Vulnerabilities (KEV) Catalog, which the agency launched in November 2021 and which now includes roughly 800 flaws that are known to have been exploited in attacks.
This year’s list also includes a “KEV count”, which represents the number of 2020 and 2021 CVEs from the catalog associated with each type of vulnerability.
MITRE says the CWE Top 25 can help a wide range of professionals mitigate risks, including software designers, developers, testers, project managers, users, educators, security researchers, and those who develop standards.
Related: National Cybersecurity Agencies List Most Exploited Vulnerabilities of 2021
Related: What We Learn From MITRE’s Most Dangerous Software Weaknesses List
Related: MITRE Publishes New List of Most Dangerous Software Weaknesses














