A cybercrime group has been targeting organizations in the hospitality sector in attacks involving fake Booking.com emails and the use of a social engineering technique named ClickFix, Microsoft warned on Thursday.
The threat actor behind these attacks is tracked by Microsoft as Storm-1865. It has been seen targeting hospitality organizations in North America, Europe, Oceania, and South and Southeast Asia in a campaign that is likely ongoing.
The hackers’ goal is to deliver information-stealing malware that enables them to conduct financial fraud and theft.
The attack starts with a fake email purporting to come from Booking.com. These messages inform the recipient — people and organizations in the hospitality sector — about negative guest reviews, account verification, online promotion opportunities, and requests from prospective guests.
The emails contain links or PDF attachments containing links that point to fake Booking.com websites that employ the ClickFix social engineering method to trick the user into downloading malware.
In the ClickFix technique, the attacker’s website displays an error or verification process that the user needs to address. The user is instructed to copy something that is not shown on the screen and then paste it into a Windows terminal and execute it.
In the Storm-1865 attacks observed by Microsoft, the victim is told to demonstrate that they are human by checking a box and pressing certain keys on their keyboard: the Windows and R keys, the CTRL and V keys, and then Enter.
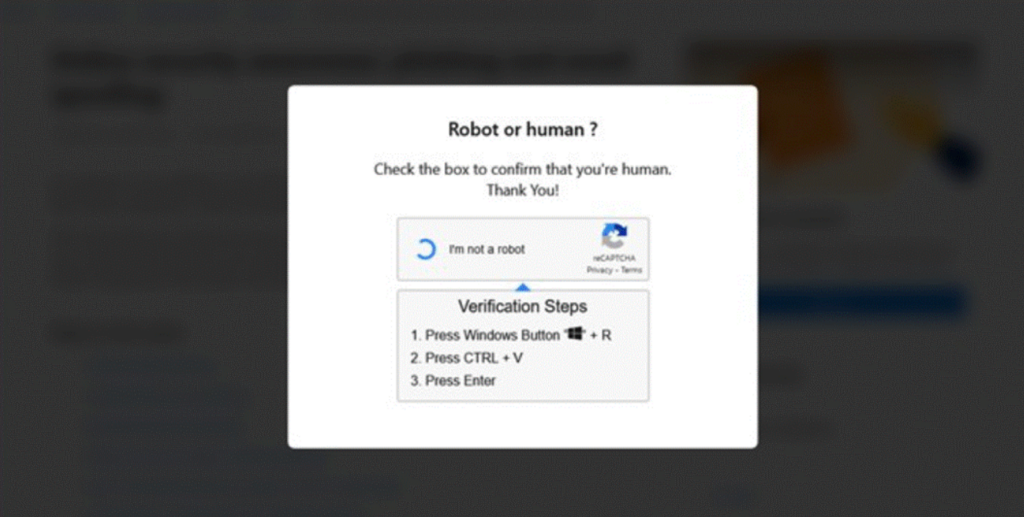
If the user complies and checks the box, they are actually copying a command into their clipboard. Pressing the key combinations opens the Windows Run command window, pastes the malicious command and executes it.
The malicious command instructs the victim’s computer to download and execute a piece of malware such as XWorm, Lumma, VenomRAT, AsyncRAT, Danabot, and NetSupport RA.
“All these payloads include capabilities to steal financial data and credentials for fraudulent use, which is a hallmark of Storm-1865 activity,” Microsoft said.
According to the tech giant, Storm-1865 has been active since 2023, conducting phishing campaigns against hotel guests and e-commerce platform users.
“The addition of ClickFix to this threat actor’s tactics, techniques, and procedures (TTPs) shows how Storm-1865 is evolving its attack chains to try to slip through conventional security measures against phishing and malware,” Microsoft said.
UPDATE: After this article was published, Booking.com provided the following statement to SecurityWeek:
“Unfortunately, phishing attacks by criminal organizations pose a significant threat to many industries. While we can confirm that Booking.com’s systems have not been breached, we are aware that unfortunately some of our accommodation partners and customers have been impacted by phishing attacks sent by professional criminals, with the criminal intent of taking over their local computer systems with malware.
The actual numbers of accommodations affected by this scam are a small fraction of those on our platform and we continue to make significant investments to limit the impact on our customers and partners.
We are also committed to proactively helping our accommodation partners and customers to stay protected. We also provide ongoing cybersecurity education and resources to our partners to enhance their defenses against such threats.”
Related: Microsoft Says One Million Devices Impacted by Infostealer Campaign
Related: Chinese Botnet Powered by 130,000 Devices Targets Microsoft 365 Accounts
Related: Microsoft Names Suspects in Lawsuit Against AI Hackers

