As part of a lawsuit targeting cybercriminals who abuse AI services, Microsoft has made public the names of four individuals who are allegedly part of a global network tracked as Storm-2139.
The lawsuit, filed in December 2024 against what Microsoft described as the ‘Azure Abuse Enterprise’, targets individuals accused of developing and using malicious tools that allow users to bypass the guardrails of gen-AI services and generate deepfakes and other harmful or illegal content.
According to Microsoft, Storm-2139 has targeted services such as its Azure OpenAI Service. The threat actors first obtain exposed credentials found in public sources, which they use to access gen-AI services. The capabilities of the targeted AI services are modified and then sold to others, with instructions on how to generate illicit content.
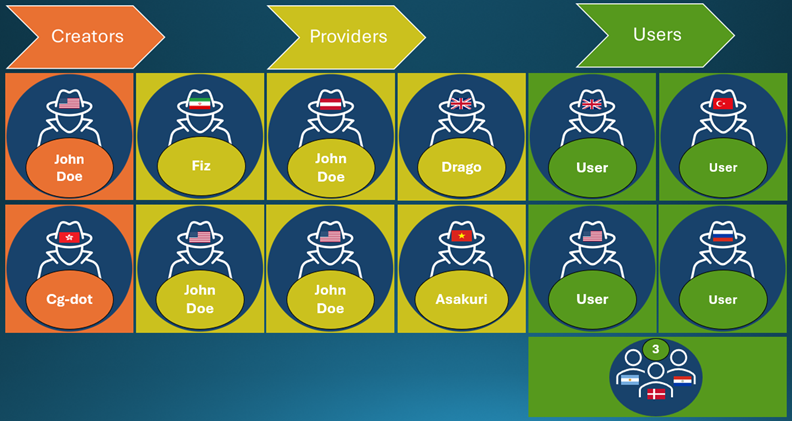
Microsoft’s investigation has revealed three types of actors involved in the Storm-2139 operation: creators, who develop the tools that allow gen-AI abuse; providers, who modify and supply these tools; and users, who use the tools to create deepfakes. According to the tech giant, the generated content is “often centered around celebrities and sexual imagery”.
The suspects named by Microsoft in a recent amended complaint are Arian Yadegarnia (Fiz) from Iran, Alan Krysiak (Drago) from the United Kingdom, Ricky Yuen (Cg-dot) from China (Hong Kong), and Phat Phung Tan (Asakuri) from Vietnam.
The company has identified over a dozen individuals involved in the operation. Of the named suspects, Cg-dot has been flagged as a creator, while Fiz, Drago, and Asakuri are believed to be providers.
Creators have been found in the US and China, while providers have been identified in countries such as Iran, Austria, Vietnam, the UK, and the United States. Users have been discovered in the US, UK, Denmark, Russia, Turkey, and South American countries.
Microsoft pointed out that two of the threat actors located in the United States are known — they live in Florida and Illinois — but their identity has not been made public to avoid interference with possible criminal investigations.
“Microsoft is preparing criminal referrals to United States and foreign law enforcement representatives,” Steven Masada, assistant general counsel in Microsoft’s Digital Crimes Unit, said in a blog post on Thursday.
Microsoft has managed to shut down a website used in the gen-AI abuse operation. After their site was taken down and the tech giant started releasing details via court documents, some of the threat actors doxed the lawyers, posting their name, personal information and even photos in some cases.
On the other hand, some of the suspected cybercriminals started revealing members’ real identities, while others contacted Microsoft’s lawyers to pin the blame on specific individuals.
Related: 2 Arrested in Takedown of Nulled, Cracked Hacking Forums


