Microsoft this week reported mitigating several massive distributed denial-of-service (DDoS) attacks aimed at its customers last year.
In October, the tech giant said one of its Azure customers had been hit in a DDoS attack that peaked at 2.4 terabits per second (Tbps), which at the time had been one of the largest attacks ever reported.
However, in November and December 2021, the company’s Azure DDoS Protection team saw even bigger attacks, including one that peaked at 3.47 Tbps and a packet rate of 340 million packets per second (pps).
This attack, aimed at one of Microsoft’s Azure customers in Asia, is believed to be the largest seen to date. The record-breaking attack was powered by 10,000 sources from around the world.
Another attack peaked at 3.25 Tbps and a third peaked at 2.55 Tbps — both attacks were aimed at unnamed organizations located in Asia.
In the second half of 2021, Microsoft mitigated nearly 2,000 DDoS attacks per day, which represented a 40% increase compared to the first half of the year. The total number of attacks aimed at the company’s customers in the second half was roughly 360,000 unique attacks.
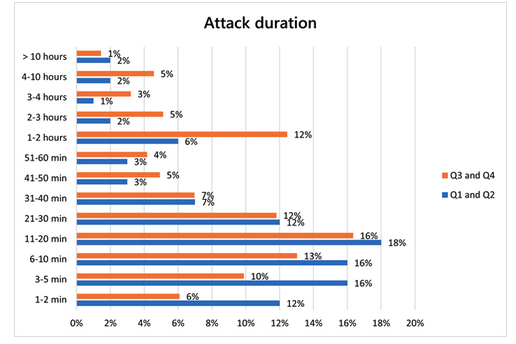
“Interestingly, there was not as much of a concentration of attacks during the end-of-year holiday season compared to previous years,” Microsoft said. “We saw more attacks in Q3 than in Q4, with the most occurring in August, which may indicate a shift towards attackers acting all year round—no longer is holiday season the proverbial DDoS season! This highlights the importance of DDoS protection all year round, and not just during peak traffic seasons.”
In terms of attack vectors, UDP attacks were the most common in the second half of 2021, accounting for 55% of attacks, followed by TCP attacks, which decreased from 54% to 19%.
The gaming industry was hit the hardest, but Microsoft reported seeing an increase in attacks on financial institutions, media, ISPs, retail and supply chain organizations.
More than half of the targeted organizations were in the United States, followed by India and East Asia.
As for duration, the tech giant reported observing a significant increase in attacks lasting more than an hour.
Related: Cloudflare Mitigated Record-Setting 17.2 Million RPS DDoS Attack

