Several companies that provide services for mitigating distributed denial-of-service (DDoS) attacks reported seeing records being broken in 2020.
In a report published on Tuesday, Akamai said it saw the largest global DDoS extortion campaign, more customers attacked than in any other previous year, the largest ever attack in terms of million packets per second (Mpps), and a record number of new customers that urgently needed protection due to an ongoing or imminent attack.
The largest attack in terms of Mpps was disclosed by the company in June — it reached 809 Mpps and it targeted a European bank. The company also saw a 1.44 terabit per second (Tbps) attack, but Amazon and Google this year reported seeing 2.3 Tbps and 2.5 Tbps attacks, respectively. The attack disclosed by Google was actually launched in 2017, but it still appears to be the largest observed to date.
Akamai also reported that it had seen more customers targeted in DDoS attacks in November 2020 than in any previous month.
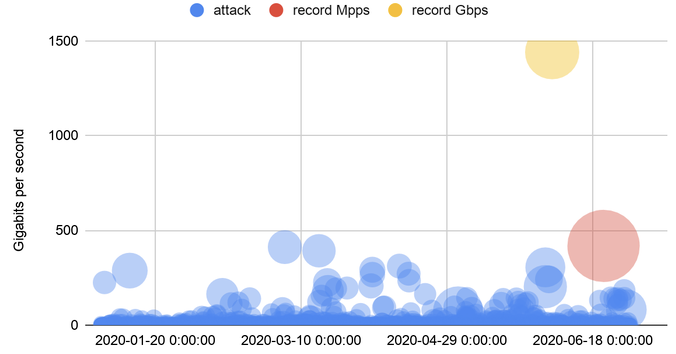
As for the major DDoS extortion campaign, the company noticed it last summer.
“This campaign featured show-of-force attacks upwards of 500 Gbps – a sign the criminals were very determined and highly capable of causing business-impacting disruption,” Akamai said. “A notable characteristic of this campaign was the level of reconnaissance conducted by the attackers prior to sending the extortion letters.”
Netscout also published some DDoS attack data on Tuesday, revealing that the number of attacks it observed last year exceeded 10 million, nearly 1.6 million more than in 2019.
“From March until the end of the year, DDoS attackers operated amidst the COVID-19 pandemic,” Netscout said. “While most of the world saw an unprecedented global health crisis, malicious actors saw new vulnerabilities and opportunity. It is seldom that annual activity is so deeply affected by one event, but such is the case with 2020 DDoS attack activity and trends. It is no coincidence that this milestone number of global attacks comes at a time when businesses have relied so heavily on online services to survive.”
“As cybercriminals quickly exploited pandemic-driven opportunities, we saw another kind of ‘new normal.’ Monthly DDoS attacks regularly exceeded 800,000 starting in March, as the pandemic lockdown took effect,” the company noted.
Kaspersky reported seeing an 88% increase in the number of DDoS attacks launched in 2020 compared to 2019.
“We suggest that this growth is caused by the pandemic and an increased reliance on web resources,” said Alexander Gutnikov, system analyst at Kaspersky’s DDoS prevention service. “For instance, in the first quarter of 2020, we identified a three-fold increase in attacks on educational and administrative resources, as they were extremely important. If people see conflicting messages about the virus and what preventive measures can be taken, they may look for official sources of information for more assured guidance. Many schools and universities also shifted to online lessons. It’s worth noting that the growth is quantitative, not qualitative: the share of sophisticated attacks that require an attacker to have skills to find the most effective attack vector has practically not changed.”
Tom Emmons, principal architect at Akamai, told SecurityWeek that they too noticed a rise in the total number of DDoS attacks launched last year, but he believes this data can be misleading “because some customers and industries are more frequently and regularly targeted by DDoS attacks – easily swaying the data depending on attacker activity.”
“The frequency of attacks was up about ~6% YOY, but the more noteworthy trends have been around the significant increase in the number of customers attacked (~22% YOY), the steady growth of attack size >50 Gbps, and the diversity of industries and verticals targeted by threat actors,” Emmons said.
Cloudflare also reported seeing some of the largest DDoS attacks in 2020.
*updated with information from Kaspersky
Related: Thousands of Unprotected RDP Servers Can Be Abused for DDoS Attacks
Related: Citrix Releases Updates to Prevent DDoS Attacks Abusing Its Appliances
Related: NXNSAttack: New DNS Vulnerability Allows Big DDoS Attacks













