At the RSA Conference in San Francisco today, Scott Charney, corporate vice president of Microsoft Trustworthy Computing, urged public and private sectors to adopt a proposal for a global Internet health model. In his keynote address about Microsoft’s Collective Defense vision, Charney said that existing technology and organizational policies could be used to implement a device health model that promotes trusted online experiences.
“We are seeing a growing alignment of social, political and economic factors. The time is right for industry, governments and individuals to focus on Internet security and privacy to help drive progress toward a safer Internet,” said Charney.
As part of the RSA keynote, Microsoft demonstrated how existing technology might be applied to an online service to encourage device health. In the scenario, a consumer chooses to opt in to a program that promotes device health by alerting the individual to a security risk identified by the web site. Notifying individuals of security problems or configuration issues in advance provides a first step in transforming current computer security posture from reactive to preventative.
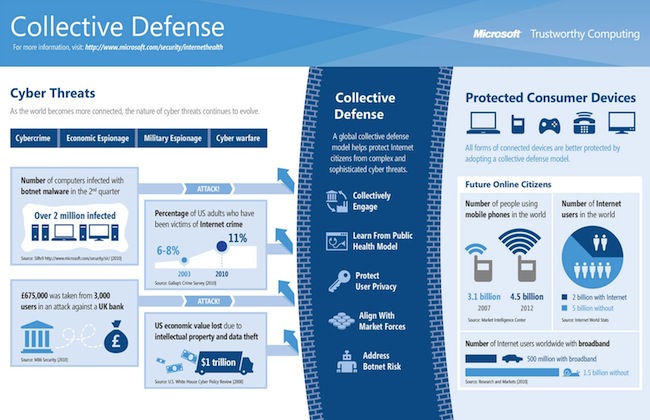
Charney cited a unique convergence of circumstances happening right now — the increased use of mobile devices and cloud computing, the persistence of botnet threats, increased public awareness of online crimes, and growing public pressure for improved government cyber security policies — that makes this the right time for industry and governments to adopt a solution that offers broad societal protections.
















