Several medical device manufacturers released security advisories this week following reports that the notorious WannaCry ransomware has infected some medical devices.
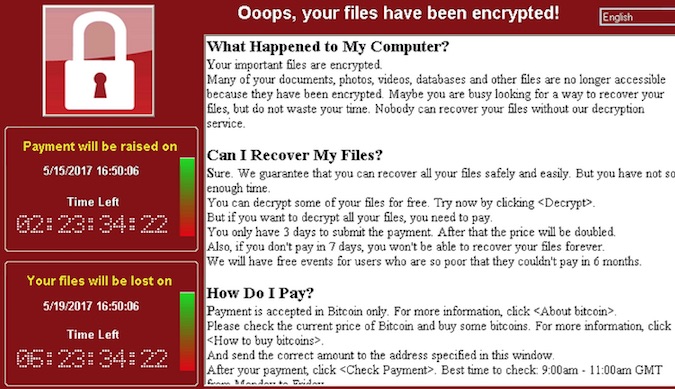
The WannaCry ransomware, also known as Wanna Decryptor, WanaCrypt0r, WannaCrypt, Wana Decrypt0r and WCry, leverages a couple of exploits allegedly developed by the NSA and leaked recently by a hacker group called Shadow Brokers. The threat has hit hundreds of thousands of systems worldwide, including ones housed by banks, hospitals, ISPs, government agencies, transportation companies and manufacturing plants.
Britain’s National Health Service (NHS) was among the worst hit by the malicious campaign, and the incident clearly showed the risk posed by WannaCry to healthcare organizations. However, initial reports suggested that the malware had mainly affected management systems.
The U.S.-based Health Information Trust Alliance (HITRUST) later reported seeing evidence of Bayer (Medrad), Siemens and other medical devices getting infected with WannaCry. Bayer confirmed for Forbes that two of its customers in the United States had informed it about ransomware infections.
Since many medical devices run on Windows and they are connected to the local network, they can easily get infected with WannaCry.
ICS-CERT has provided a list of vendors that have released security advisories to warn customers of the risks and provide them with recommendations on how to prevent attacks.
The list includes Rockwell Automation, BD (Becton, Dickinson and Company), Schneider Electric, ABB, Siemens, General Electric, Philips, Smiths Medical, Johnson & Johnson, and Medtronic. Some of these vendors have also issued warnings about the threat posed to their industrial products.
Related: Industry Reactions to WannaCry Ransomware Attacks
BD has published a list of tens of potentially vulnerable devices and provided recommendations for securing Windows-based systems. Siemens has released separate advisories for each affected Healthineers product, including magnetic resonance, laboratory diagnostics, tomography, radiography, X-ray, mammography, molecular diagnostics, and molecular imaging devices.
Siemens says it’s working on updates that will patch Server Message Block (SMB) vulnerabilities in affected products, and shared some countermeasures until fixes become available. WannaCry exploits one particular SMB vulnerability patched by Microsoft in March, but the fix for this flaw also addresses several other SMB weaknesses.
Other medical device vendors have not listed affected products, but warned customers that all Windows-based systems are at risk. Some highlighted that they had not been aware of any incidents involving their products.
“The WannaCry medical device infections show that data isn’t the only digital asset being targeted. They further demonstrate that if these devices can be impacted, so too can mission-critical infrastructures, industrial IoT devices and control systems. When one of these targets falls prey to ransomware, the outcome could be catastrophic — measured in terms of human injury and lives as opposed to just a few bitcoins,” said Dean Weber, CTO of industrial IoT security provider Mocana.
“IT, OT and security professionals in hospitals and other mission critical environments should act immediately to patch systems, especially those running Windows. They should also consider taking proactive steps that could include adding multi-factor authentication, stronger encryption and embedding security directly into devices to establish more effective trust,” Weber concluded.
Related: PATCH Act – A New Bill Designed to Prevent Occurrences Like WannaCrypt
Related: Microsoft Withheld Update That Could Have Slowed WannaCry














