Kaspersky Lab products installed on industrial automation systems have detected over 19,000 malware samples in the first half of 2018, and the company has determined that the Internet is an increasingly significant source of attacks.
According to Kaspersky’s “Threat Landscape for Industrial Automation Systems” report for H1 2018, the company detected over 19,400 samples belonging to roughly 2,800 malware families. As expected, most of the attempts to infect industrial systems were part of random attacks rather than targeted operations.
An overall increase in malicious activity has led to attack attempts against 41.2% of the industrial control systems (ICS) protected by the security firm, which represents an increase of nearly 5 percentage points compared to the first half of 2017. Kaspersky detected 18,000 malware samples belonging to more than 2,500 families in that period.
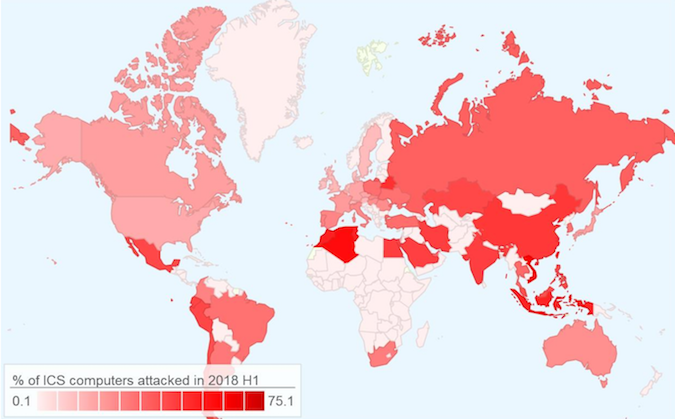
Attacks were reported all around the world, but Asian, Latin American and North African countries had the highest percentage of attacked ICS computers, with up to 75% of devices targeted. In the United States, only 21.4% of industrial systems were targeted. Kaspersky noted that developed countries had recorded fewer attacks compared to ones with a low per capita GDP.
A majority of the detected threats were Trojans using either Windows or web browsers as a platform.
“In H1 2018, threat actors continued to attack legitimate websites that had vulnerabilities in their web applications in order to host malware components on these websites,” Kaspersky said in its report. “Notably, the increase in the percentage of ICS computers attacked through browsers in H1 2018 was due to the increase in the number of attacks that involved JavaScript cryptocurrency miners. At the same time, the increase in the number of ICS computers attacked using Microsoft Office documents was associated with waves of phishing emails.”
Register for SecurityWeek’s 2018 ICS Cyber Security Conference
The security firm determined that the Internet was the source in 27.3% of attacks, which represents an increase of nearly 7 percentage points compared to the same period of last year. Removable media accounted for 8.4% and email clients for 3.8% of attacks, with no significant changes compared to the prior period.
“This pattern seems logical: modern industrial networks can hardly be considered isolated from external systems. Today, an interface between the industrial network and the corporate network is needed both to control industrial processes and to provide administration for industrial networks and systems,” Kaspersky said.
Asia, Africa and Latin America are not only the most targeted, but they also represent the main sources of threats blocked by Kaspersky’s products.
Related: Five Threat Groups Target Industrial Systems
Related: DHS Warns of Malware Targeting Industrial Safety Systems















