In mid July, Seculert discovered a new cyber-espionage weapon that was targeting organizations in the Middle East.
Known as ‘Mahdi‘ or ‘Madi’, the malware is capable of stealing data from infected Windows computers, and also capable of monitoring email and instant messages, recording audio, capturing keystrokes and taking screenshots of victims’ computers.
Overall, Mahdi is a complex cyber-espionage weapon that unlike Flame, Stuxnet and Gauss, is still alive and well, and continues to get updated and find new targets.
According to new research from Seculert, the group behind Mahdi continues to test and improve new versions of the malware in order to find ways to evade security measures.
Israel-based Seculert says that in the past few weeks, they have monitored dozens of new variants of Mahdi, many of which are not currently being detected by most AV vendors.
Additionally, Seculert says that since the initial discovery of the malware back in July, 150 new Mahdi victims have been identified, with the total number of infections identified approaching 1,000 globally.
Some of these targets appear to be located in the United States and in Germany, Seculert said, though most targets still appear to be from Iran.
“This correlates back to the fact that the latest version of Mahdi, added new triggers to the malware – ‘USA’ and ‘GOV’,” the company explained in a blog post.
For those organizations being targeted in the US, the victims have connections to Middle Eastern companies, either working at such companies, or visit them frequently, a Seculert spokesperson told SecurityWeek.
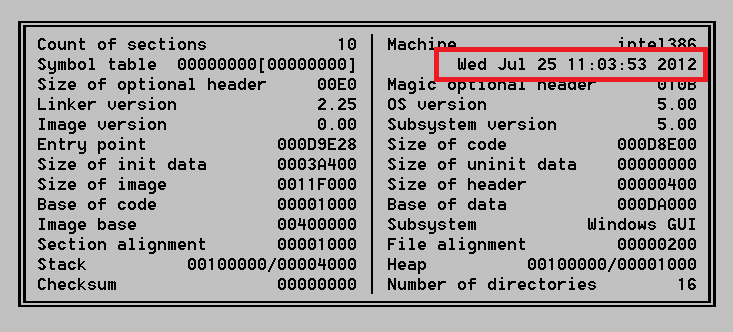
Seculert also explained that after investigating a fifth command and control (C&C) server since the initial discovery of Mahdi, they were able to identify different malware variants communicating with it dating back to June 2012. That firth server, located in Canada, seems to have replaced the original server that was identified in back in February.















