Kaspersky Lab and Seculert revealed the presence today of a new cyber-espionage weapon known targeting users in the Middle East.
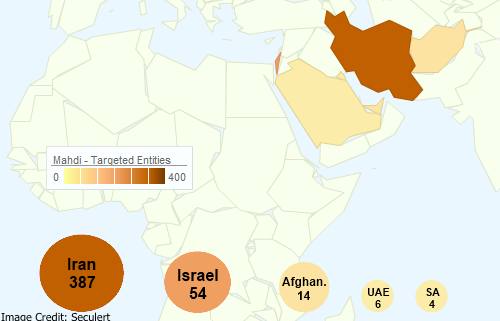
The malware, known as ‘Mahdi‘ or ‘Madi‘, was originally discovered by Seculert. In addition to stealing data from infected Windows computers, it is also capable of monitoring email and instant messages, recording audio, capturing keystrokes and taking screenshots of victims’ computers. Working together, researchers at Seculert and Kaspersky sinkholed the malware’s command and control servers and monitored the campaign. What they found was a targeted attack that impacted more than 800 victims in Iran, Israel and other countries from around the globe.
Statistics from the sinkhole revealed many of the victims were business people working on Iranian and Israeli critical infrastructure projects, Israeli financial institutions, Middle Eastern engineering students or various government agencies in the region. All totaled, multiple gigabytes of data are believed to have been uploaded from victims’ computers.
 “The targeted organizations seem to be spread between members of the attacking group by giving each victim machine a specific prefix name, meaning that this operation might require a large investment and financial backing,” according to Seculert.
“The targeted organizations seem to be spread between members of the attacking group by giving each victim machine a specific prefix name, meaning that this operation might require a large investment and financial backing,” according to Seculert.
According to Seculert, it is unclear whether or not the Trojan is part of a state-sponsored attack, and no evidence has been found of any connection to Flame. However, there may be potential clues to its origins hidden in the code.
“Interestingly, our joint analysis uncovered a lot of Persian strings littered throughout the malware and the C&C tools, which is unusual to see in malicious code,” noted Aviv Raff, chief technology officer at Seculert, in a statement. “The attackers were no doubt fluent in this language.”
To infect computers, the attackers relied on social engineering ploys designed to get users to open up PowerPoint slideshows containing the malicious file. Some of the more common applications and websites that were spied on included accounts for Gmail, Hotmail, Yahoo! Mail, ICQ, Skype, Google+ and Facebook. Surveillance is also performed over integrated ERP/CRM systems, business contracts, and financial management systems, according to the researchers.
“This latest malware does not show signs of being complex and expensive, but the relative simplicity of the weapon (compared, say, to Flame) does not mean it’s less effective at reaching its goals,” said RedSeal CTO Mike Lloyd. “Globally, our infrastructure is weak – there have been steady increases in complexity, and networks continue to become more interdependent. Research shows that easy attacks work, and are at the core of the majority of detected breaches.”
Technical analysis from Kaspersky can be read here.

