Leaked documents appear to show a little-known spyware company offering services that include Android and iOS device exploits for €8 million (roughly $8 million).
Exploit brokers and mercenary spyware providers have been in the spotlight recently, mainly due to revelations surrounding the use of the controversial Pegasus solution of Israeli company NSO Group.
One of NSO’s fairly new competitors is Intellexa, a company founded by Israeli entrepreneur Tal Dilian. The company claims on its website that it’s offering technologies that empower law enforcement and intelligence agencies to ‘help protect communities’. The company says it’s based in the EU and regulated, with six sites and R&D labs in Europe.
Vx-undergroud, which provides malware source code and other cybersecurity resources, posted some screenshots on Twitter on Wednesday showing several documents apparently representing a commercial proposal from Intellexa.
The documents, labeled as proprietary and confidential, describe services for remote data extraction from Android and iOS devices. Specifically, the offering is for remote, one-click browser-based exploits that allow users to inject a payload into Android or iOS mobile devices. The brief description suggests that the victim has to click on a link for the exploit to be delivered.
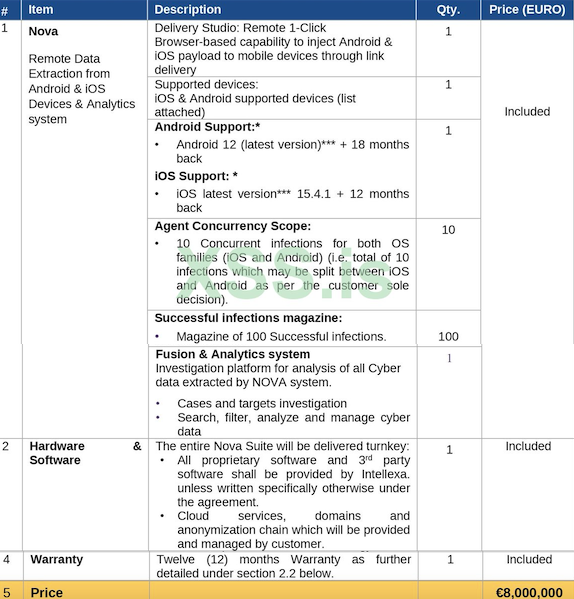
The offer includes 10 concurrent infections for iOS and Android devices, as well as a “magazine of 100 successful infections”. The leaked documents also show a partial list of Android devices against which an attack would supposedly work.
The documents say the exploits should work on iOS 15.4.1 and the latest Android 12 update.
Apple released iOS 15.4.1 in March, which suggests that the offer is fairly recent. Three security updates have been released since for the mobile operating system. This means Apple may have patched one or more of the zero-day vulnerabilities used by the Intellexa iOS exploit, but it’s also possible for the exploits offered by these types of companies to remain unpatched for a long time.
While some have described the $8 million as the price of an iOS exploit, the customer would actually get much more for the price. The offer is for an entire platform that includes capabilities to analyze the data extracted by the exploits, as well as a 12-month warranty.
The documents are not dated, but vx-undergroud said the screenshots were posted on the Russian-language hacker forum XSS on July 14.
While there is a lot of technical information available on the exploits offered by spyware companies, not much is known about what they charge customers. The New York Times reported in 2016 that the NSO Group had charged customers $500,000 to install its software and $650,000 to hack 10 devices. India’s Economic Times reported in 2019 that a Pegasus license cost roughly $7-8 million per year.
It’s also known that exploit brokers are prepared to pay as much as $2 million for full chain Android and iOS exploits that do not require any user interaction.
Intellexa was mentioned last year in a Citizen Lab report on Cytrox’s Predator iPhone spyware being used to target a Greek lawmaker. Citizen Lab said Cytrox was part of the Intellexa Alliance, which it described as a “a marketing label for a range of mercenary surveillance vendors that emerged in 2019”.
SecurityWeek has reached out to Intellexa, Apple and Google for comment.
Apple filed a lawsuit last year against NSO Group in an effort to ban the company from using its software, services or devices.
Related: Apple, Android Phones Targeted by Italian Spyware: Google
Related: FBI Confirms It Bought Spyware From Israel’s NSO Group

