An Iran-linked cyberespionage group tracked as APT33 has used obfuscated botnets as part of attacks aimed at high-value targets located in the United States, the Middle East and Asia, Trend Micro reported on Thursday.
APT33, which some experts believe has been active since at least 2013, is also known as Refined Kitten, Elfin, Magnallium and Holmium. It has targeted organizations in the government, research, aerospace, energy, oil, consulting, finance, telecoms, manufacturing and chemical sectors in the United States, Europe, the Middle East and Asia.
Researchers at Trend Micro have been monitoring the threat actor’s activities and noticed that while some attacks are “relatively noisy,” some high-value entities have been targeted using a dedicated infrastructure set up to make tracking more difficult.
This infrastructure has been used this year against several targets in the United States, including a private company offering services related to national security, a college, a university, and an entity related to the military. Several victims were also observed in the Middle East and Asia.
As part of these attacks, APT33 has used small botnets, each comprised of roughly a dozen bots (i.e. compromised machines on the victim’s network). Trend Micro says these bots are used to gain persistence on the network and the malware on these devices is basic — it allows attackers to download and run additional tools.
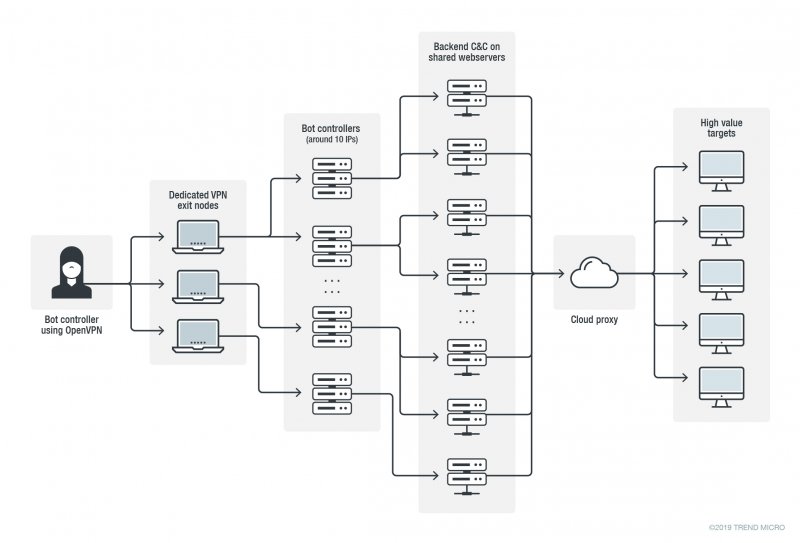
The attackers have set up several command and control (C&C) domains on cloud-hosted proxies that relay requests from bots to backend C&C servers hosted on shared web servers, which may also host thousands of legitimate domains.
These backends send bot data to aggregator and bot control servers that have dedicated IP addresses. The attackers use a private VPN network to connect to these aggregator servers, including when they collect data from the bots and when they issue commands to the bots.
“In fall of 2019 we counted 10 live bot data aggregating and bot controlling servers and tracked a couple of them for months. These aggregators get data from very few C&C servers (only 1 or 2), with only up to a dozen victims per unique C&C domain,” Trend Micro said in a blog post.
While setting up a private VPN network might have some benefits for the attackers, the cybersecurity firm says it has actually made it easier for its researchers to track APT33’s traffic.
Tracking the group’s private VPN exit nodes for over a year has allowed Trend Micro to determine that the attackers have also used the same VPN network for reconnaissance activities aimed at the oil industry supply chain, for accessing email and cryptocurrency websites, and reading hacking blogs and forums.
Given APT33’s interest in the oil industry — Trend Micro says the hackers have also visited sites used to recruit people in the oil and gas sector — companies have been advised to check their security logs for the IP addresses known to have been used by the threat actor.
Recorded Future revealed in June that APT33 had updated its infrastructure after a report detailing its activities was published in March.
Related: U.S. Cyber Command Warns of Outlook Flaw Exploited by Iranian Hackers
Related: WinRAR Vulnerability Exploited to Deliver New Malware
Related: Iranian Hackers Caused Losses in Hundreds of Millions: Report

