Over 230 Vulnerabilities Patched in Intel Products in 2020
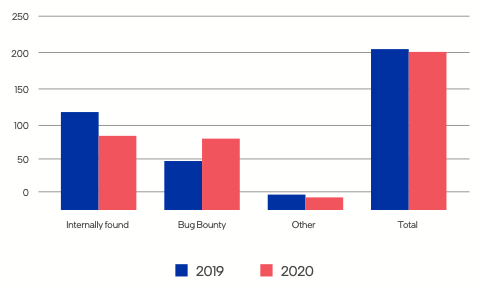
Intel patched 231 vulnerabilities in its products last year, roughly the same as in the previous year, when it fixed 236 flaws.
The chipmaker on Wednesday published its 2020 Product Security Report, which reveals that nearly half of the vulnerabilities patched last year were discovered by its own employees, and the company claims that a vast majority of the addressed issues are the direct result of its investment in product security assurance.
According to Intel, 105 vulnerabilities were reported through the company’s bug bounty program, which saw a 33% increase in submissions compared to the previous year. The company also reported seeing a significant increase in the number of external security researchers it engaged with.
Intel said it paid out an average of $800,000 per year through its bug bounty program since it was launched in 2018.
The report shows that 93 vulnerabilities were found in software, 66 in firmware, and 58 required both firmware and software updates to patch. Fourteen flaws were found to affect hardware.
In terms of severity, only 3% of the security holes patched last year were rated critical. Roughly one-third were rated high severity, and 57% were assigned a medium severity rating.
“The impact of most of the medium, high, and critical vulnerabilities is potential elevation of privilege,” Intel explained in its report. “In the case of medium severity issues, these require an authenticated user on the same physical network or who has physical access to a vulnerable system. These issues become high or critical, if an unauthenticated user can trigger the vulnerability and/or they can reach a vulnerable system from outside the local area network.”
Related: Intel Patches Tens of Vulnerabilities in Software, Hardware Products
Related: Intel Releases Firmware Updates to Patch Critical Vulnerability in AMT, ISM
Related: Vulnerability in Intel Chipsets Allows Hackers to Obtain Protected Data
Related: Load Value Injection: Intel CPUs Vulnerable to Reverse Meltdown Attack












