Security experts believe hackers will soon start to remotely exploit the recently disclosed vulnerabilities affecting Intel, AMD and ARM processors, if they haven’t done so already.
Researchers disclosed on Wednesday the details of Spectre and Meltdown, two new attack methods targeting CPUs. The attacks leverage three different flaws and they can be used to bypass memory isolation mechanisms and gain access to sensitive data, including passwords, photos, documents, and emails.
The affected CPUs are present in billions of products, including PCs and smartphones, and attacks can also be launched against cloud environments.
The best protection against these attacks is the use of kernel page table isolation (KPTI) and affected vendors have already started releasing patches and workarounds.
While the main attack vector is via local access (e.g. a piece of malware installed on the targeted machine), researchers say remote attacks via JavaScript are also possible, particularly in the case of Spectre.
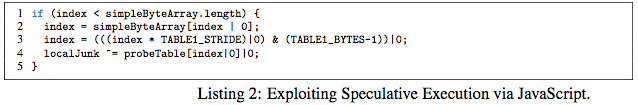
Researchers have developed a proof-of-concept (PoC) for Google Chrome that uses JavaScript to exploit Spectre and read private memory from the process in which it runs.
Mozilla has conducted internal experiments and determined that these techniques can be used “from Web content to read private information between different origins.” While the issue is still under investigation, the organization has decided to implement some partial protections in Firefox 57.
Google pointed out that attacks are possible via both JavaScript and WebAssembly. The company informed customers that current versions of Chrome include a feature named Site Isolation that can be manually enabled to prevent attacks. Chrome 64, which is scheduled for release on January 23, will contain mitigations in the V8 JavaScript engine. Other hardening measures will be included in future versions, but the tech giant warned that they may have a negative impact on performance.
Microsoft has also confirmed that attacks can be launched via JavaScript code running in the browser. The company has released updates for its Edge and Internet Explorer web browsers to mitigate the vulnerabilities.
Since a JavaScript PoC is available, experts believe it’s only a matter of time until malicious actors start exploiting the flaws remotely. While some say state-sponsored actors are most likely to leverage these attacks, others point out that mass exploitation is also possible, particularly via the ads served by websites.
That is why some experts have advised users to disable JavaScript in their browser and install ad blockers.
Mike Buckbee, security engineer at Varonis, noted that while exploitation via the browser might not give attackers access to files, they are still likely to find valuable data in the memory, including SSH keys, security tokens and passwords.
While affected vendors say there is no evidence that Spectre and Meltdown have been exploited prior to their disclosure, the researchers who discovered the vulnerabilities warn that attacks are not easy to detect.
Researcher Jake Williams said, “It’s reasonable to assume that most nation states had Spectre and Meltdown before public announcement. If by some miracle they weren’t already using these, they will be now.”
Bryce Boland, Asia Pacific Chief Technology Officer at FireEye, agrees. “Nation state hackers typically use these types of vulnerabilities to develop new attack tools, and that’s likely in this case,” he said.
Sam Curry, Chief Security Officer at Cybereason, also believes sophisticated actors will likely exploit the flaws, if they haven’t done so already.
“This isn’t yet doom and gloom but the tension will rise. And don’t be surprised if it comes to light that a nation state is already using this or if a catalyst in the form of hack or research further heats this up and makes it a more clear-and-present risk in 2018,” Curry told SecurityWeek.













