An open source tool named Kamerka allows users to generate a map of Internet-exposed industrial control systems (ICS) in a specified country and link results to Google Street View.
Launched in November 2018 by a researcher who uses the online moniker Wojciech, Kamerka was initially designed to identify nearby surveillance cameras exposed to the Internet. It was later updated with capabilities allowing users to also generate a map of Flickr and Instagram photos, printers, and Twitter messages.
The tool uses Shodan, Geopy, Folium and other services to display an interactive map of the identified systems.
The latest update made by Wojciech to Kamerka allows users to generate a map of exposed ICS in any country and link them to Google Street View.
“If you believe you have found place where industrial control systems are running, you can examine its physical security. By this I mean entrances of the building, windows, security cameras or parking lots nearby. It’s good to have a tool for red team assessments to plan operations,” the researcher explained.
The ICS part of the tool uses Shodan, Folium and the Google Street View API to create a map with images from Street View. It looks for various types of products and protocols, including Siemens S7, Tridium, General Electric, Omron, PCWorx, Red Lion, CodeSys, ProConOS, Modbus, BACnet, HART IP, DNP3, Ethernet/IP, and IEC 60870–5–104.
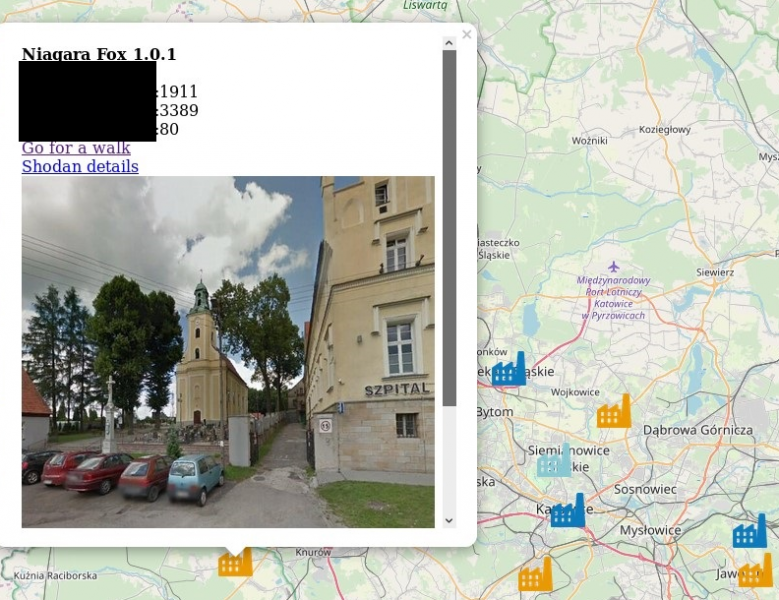
The researcher has pointed out that while a majority of the identified devices appear to be housed by unidentified buildings, he has found some exposed systems in hospitals and even power plants.
Learn More About Exposed Industrial Systems at SecurityWeek’s 2019 ICS Cyber Security Conference
In addition to allowing users to see images of the buildings housing the exposed systems, Kamerka provides information on the web server associated with each device, including login pages served over HTTP.
“Attack or defense, both sides need good intelligence, especially when fragile and very sensitive systems like ICS are in play,” Wojciech explained. “Functioning of the city/country depends on these devices and lives may be in danger in case of outages or intentional cyber-destruction. That’s why it is important to monitor every device connected to the internet which might pose a risk to the factories, plants, hospitals, airplanes or other important structures of the country.”
Related: New Shodan Service Keeps Track of Internet-Exposed Systems
Related: Internet-Exposed HMIs Put Energy, Water Facilities at Risk
Related: Refrigeration Systems Used by Supermarkets, Hospitals Left Exposed Online
















